An operating system acts as an intermediary between the user of a computer and computer hardware. The purpose of an operating system is to provide an environment in which a user can execute programs conveniently and efficiently.
An operating system is software that manages computer hardware. The hardware must provide appropriate mechanisms to ensure the correct operation of the computer system and to prevent user programs from interfering with the proper operation of the system. A more common definition is that the operating system is the one program running at all times on the computer (usually called the kernel), with all else being application programs.
An operating system is concerned with the allocation of resources and services, such as memory, processors, devices, and information. The operating system correspondingly includes programs to manage these resources, such as a traffic controller, a scheduler, a memory management module, I/O programs, and a file system.
History of Operating System
The operating system has been evolving through the years. The following table shows the history of OS.
| First |
1945-55 |
Vacuum Tubes |
Plug Boards |
| Second |
1955-65 |
Transistors |
Batch Systems |
| Third |
1965-80 |
Integrated Circuits(IC) |
Multiprogramming |
| Fourth |
Since 1980 |
Large Scale Integration |
PC |
Characteristics of Operating Systems
Let us now discuss some of the important characteristic features of operating systems:
- Device Management: The operating system keeps track of all the devices. So, it is also called the Input/Output controller that decides which process gets the device, when, and for how much time.
- File Management: It allocates and de-allocates the resources and also decides who gets the resource.
- Job Accounting: It keeps track of time and resources used by various jobs or users.
- Error-detecting Aids: These contain methods that include the production of dumps, traces, error messages, and other debugging and error-detecting methods.
- Memory Management: It keeps track of the primary memory, like what part of it is in use by whom, or what part is not in use, etc. and It also allocates the memory when a process or program requests it.
- Processor Management: It allocates the processor to a process and then de-allocates the processor when it is no longer required or the job is done.
- Control on System Performance: It records the delays between the request for a service and the system.
- Security: It prevents unauthorized access to programs and data using passwords or some kind of protection technique.
- Convenience: An OS makes a computer more convenient to use.
- Efficiency: An OS allows the computer system resources to be used efficiently.
- Ability to Evolve: An OS should be constructed in such a way as to permit the effective development, testing, and introduction of new system functions at the same time without interfering with service.
- Throughput: An OS should be constructed so that It can give maximum throughput (Number of tasks per unit time).
Functionalities of Operating System
- Resource Management: When parallel accessing happens in the OS means when multiple users are accessing the system the OS works as Resource Manager, Its responsibility is to provide hardware to the user. It decreases the load in the system.
- Process Management: It includes various tasks like scheduling and termination of the process. It is done with the help of CPU Scheduling algorithms.
- Storage Management: The file system mechanism used for the management of the storage. NIFS, CIFS, CFS, NFS, etc. are some file systems. All the data is stored in various tracks of Hard disks that are all managed by the storage manager. It included Hard Disk.
- Memory Management: Refers to the management of primary memory. The operating system has to keep track of how much memory has been used and by whom. It has to decide which process needs memory space and how much. OS also has to allocate and deallocate the memory space.
- Security/Privacy Management: Privacy is also provided by the Operating system using passwords so that unauthorized applications can’t access programs or data. For example, Windows uses Kerberos authentication to prevent unauthorized access to data.
The process operating system as User Interface:
- User
- System and application programs
- Operating system
- Hardware
Every general-purpose computer consists of hardware, an operating system(s), system programs, and application programs. The hardware consists of memory, CPU, ALU, I/O devices, peripheral devices, and storage devices. The system program consists of compilers, loaders, editors, OS, etc. The application program consists of business programs and database programs.
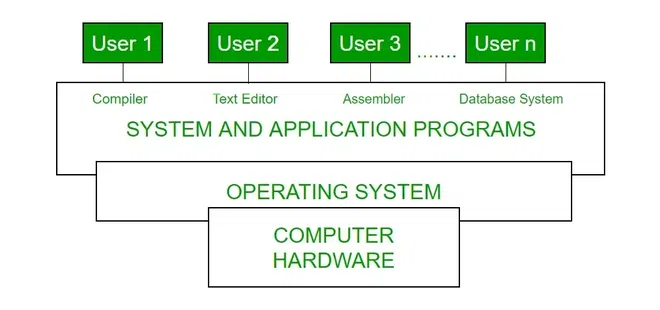
Conceptual View of Computer System
Every computer must have an operating system to run other programs. The operating system coordinates the use of the hardware among the various system programs and application programs for various users. It simply provides an environment within which other programs can do useful work.
The operating system is a set of special programs that run on a computer system that allows it to work properly. It performs basic tasks such as recognizing input from the keyboard, keeping track of files and directories on the disk, sending output to the display screen, and controlling peripheral devices.
Layered Design of Operating System

Fig. Layered OS
The extended machine provides operations like context save, dispatching, swapping, and I/O initiation. The operating system layer is located on top of the extended machine layer. This arrangement considerably simplifies the coding and testing of OS modules by separating the algorithm of a function from the implementation of its primitive operations. It is now easier to test, debug, and modify an OS module than in a monolithic OS. We say that the lower layer provides an abstraction that is the extended machine. We call the operating system layer the top layer of the OS.
Purposes and Tasks of Operating Systems
Several tasks are performed by the Operating Systems and it also helps in serving a lot of purposes which are mentioned below. We will see how Operating System helps us in serving in a better way with the help of the task performed by it.
Purposes of an Operating System
- It controls the allocation and use of the computing System’s resources among the various user and tasks.
- It provides an interface between the computer hardware and the programmer that simplifies and makes it feasible for coding and debugging of application programs.
Tasks of an Operating System
- Provides the facilities to create and modify programs and data files using an editor.
- Access to the compiler for translating the user program from high-level language to machine language.
- Provide a loader program to move the compiled program code to the computer’s memory for execution.
- Provide routines that handle the details of I/O programming.
I/O System Management
The module that keeps track of the status of devices is called the I/O traffic controller. Each I/O device has a device handler that resides in a separate process associated with that device.
The I/O subsystem consists of
- A memory Management component that includes buffering caching and spooling.
- A general device driver interface.
Drivers for Specific Hardware Devices
Below mentioned are the drivers which are required for a specific Hardware Device. Here we discussed Assemblers, compilers, and interpreters, loaders.
Assembler
The input to an assembler is an assembly language program. The output is an object program plus information that enables the loader to prepare the object program for execution. At one time, the computer programmer had at his disposal a basic machine that interpreted, through hardware, certain fundamental instructions. He would program this computer by writing a series of ones and Zeros (Machine language) and placing them into the memory of the machine. Examples of assembly languages include
Compiler and Interpreter
The High-level languages– examples are C, C++, Java, Python, etc (around 300+ famous high-level languages) are processed by compilers and interpreters. A compiler is a program that accepts a source program in a “high-level language “and produces machine code in one go. Some of the compiled languages are FORTRAN, COBOL, C, C++, Rust, and Go. An interpreter is a program that does the same thing but converts high-level code to machine code line-by-line and not all at once. Examples of interpreted languages are
Loader
A Loader is a routine that loads an object program and prepares it for execution. There are various loading schemes: absolute, relocating, and direct-linking. In general, the loader must load, relocate and link the object program. The loader is a program that places programs into memory and prepares them for execution. In a simple loading scheme, the assembler outputs the machine language translation of a program on a secondary device and a loader places it in the core. The loader places into memory the machine language version of the user’s program and transfers control to it. Since the loader program is much smaller than the assembler, those make more core available to the user’s program.
Components of an Operating Systems
There are two basic components of an Operating System.
Shell
Shell is the outermost layer of the Operating System and it handles the interaction with the user. The main task of the Shell is the management of interaction between the User and OS. Shell provides better communication with the user and the Operating System Shell does it by giving proper input to the user it also interprets input for the OS and handles the output from the OS. It works as a way of communication between the User and the OS.
Kernel
The kernel is one of the components of the Operating System which works as a core component. The rest of the components depends on Kernel for the supply of the important services that are provided by the Operating System. The kernel is the primary interface between the Operating system and Hardware.
Functions of Kernel
The following functions are to be performed by the Kernel.
- It helps in controlling the System Calls.
- It helps in I/O Management.
- It helps in the management of applications, memory, etc.
Types of Kernel
There are four types of Kernel that are mentioned below.
For more, refer to Kernel in Operating System.
Difference Between 32-Bit and 64-Bit Operating Systems
| 32-Bit OS is required for running of 32-Bit Processors, as they are not capable of running on 64-bit processors. |
64-Bit Processors can run on any of the Operating Systems, like 32-Bit OS or 64-Bit OS. |
| 32-Bit OS gives a low efficient performance. |
64-Bit Operating System provides highly efficient Performance. |
| Less amount of data is managed in 32-Bit Operating System as compared to 64-Bit Os. |
A large amount of data can be stored in 64-Bit Operating System. |
| 32-Bit Operating System can address 2^32 bytes of RAM. |
64-Bit Operating System can address 2^64 bytes of RAM. |
The fundamental goals of operating system are:
- Efficient use: Ensure efficient use of a computer’s resources.
- User convenience: Provide convenient methods of using a computer system.
- Non interference: Prevent interference in the activities of its users.
- Efficient use:
An operating system must ensure efficient use of the fundamental computer system resources of memory, CPU, and I/O devices such as disks and printers. Poor efficiency can result if a program does not use a resource allocated to it. Efficient use of resources can be obtained by monitoring use of resources and performing corrective actions when necessary. However, monitoring use of resources increases the overhead, which lowers efficiency of use. In practice, operating systems that emphasize efficient use limit their overhead by either restricting their focus to efficiency of a few important resources, like the CPU and the memory, or by not monitoring the use of resources at all, and instead handling user programs and resources in a manner that guarantees high efficiency.
2.User convenience:
In the early days of computing, user convenience was synonymous with bare necessity—the mere ability to execute a program written in a higher level language was considered adequate. Experience with early operating systems led to demands for better service, which in those days meant only fast response to a user request. Other facets of user convenience evolved with the use of computers in new fields. Early operating systems had command-line interfaces, which required a user to type in a command and specify values of its parameters. Users needed substantial training to learn use of the commands, which was acceptable because most users were scientists or computer professionals. However, simpler interfaces were needed to facilitate use of computers by new classes of users. Hence graphical user interfaces (GUIs) were evolved. These interfaces used icons on a screen to represent programs and files and interpreted mouse clicks on the icons and associated menus as commands concerning them. In many ways, this move can be compared to the spread of car driving skills in the first half of the twentieth century. Over a period of time, driving became less of a specialty and more of a skill that could be acquired with limited training and experience.
3.Non interference:
A computer user can face different kinds of interference in his computational activities. Execution of his program can be disrupted by actions of other persons, or the OS services which he wishes to use can be disrupted in a similar manner. The OS prevents such interference by allocating resources for exclusive use of programs and OS services, and preventing illegal accesses to resources. Another form of interference concerns programs and data stored in user files.
Advantages of Operating System
- It helps in managing the data present in the device i.e. Memory Management.
- It helps in making the best use of computer hardware.
- It helps in maintaining the security of the device.
- It helps different applications in running them efficiently.
Disadvantages of Operating System
- Operating Systems can be difficult for someone to use.
- Some OS are expensive and they require heavy maintenance.
- Operating Systems can come under threat if used by hackers.
FAQs on Operating Systems
Q.1: Explain Operating System.
Answer:
The operating system can be explained as the intermediate, which works between the user and the system hardware so that the user can get a nice experience while using a system. Without an Operating system, there will be a lot of difficulties can be faced by the user while running a system.
Q.2: What are the types of operating Systems?
Answer:
The types of Operating systems are listed below.
Q.3: What is the importance of an Operating System?
Answer:
The operating system is one of the most important parts of a Computer System. Without an Operating System, the system will not be able to work. As Operating System works as an interpreter between the user and the hardware part, which helps in the smooth functioning of the system.
Q.4: What is an OS Structure?
Answer:
Operating System structure is basically the model in which the system works. The structure of the operating system should be user-friendly, such that if any user having less knowledge about the system comes then he/she will not face any difficulties while running the system.
Q.5: What do you mean by a process in Operating System?
Answer:
A process can be simply defined as the instance of a computer. The process always includes the program code and its operations both. The process also includes the threads running in the computer system. It can be a single thread or a multiple thread.
Share your thoughts in the comments
Please Login to comment...