Nmap Command in Linux with Examples
Last Updated :
10 Mar, 2023
Nmap is Linux command-line tool for network exploration and security auditing. This tool is generally used by hackers and cybersecurity enthusiasts and even by network and system administrators. It is used for the following purposes:
- Real time information of a network
- Detailed information of all the IPs activated on your network
- Number of ports open in a network
- Provide the list of live hosts
- Port, OS and Host scanning
Installing Nmap Command
In case of Debian/Ubuntu
sudo apt-get install nmap
In case of CentOS/RedHat
yum install nmap
Working with Nmap Command
1. To scan a System with Hostname and IP address. First, Scan using Hostname
nmap www.geeksforgeeks.org
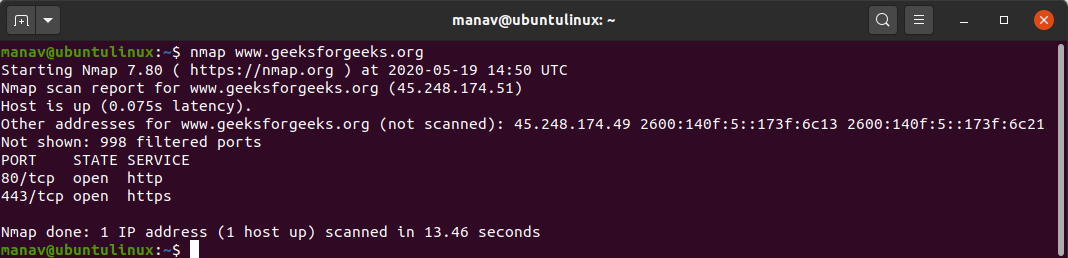
Now let’s Scan using IP Address
nmap 172.217.27.174
The nmap command allows scanning a system in various ways. In this we are performing a scan using the hostname as “geeksforgeeks” and IP address “172.217.27.174”, to find all open ports, services, and MAC addresses on the system.
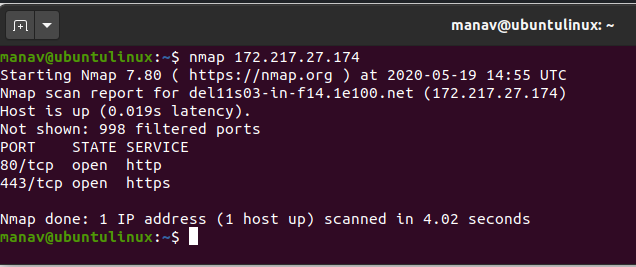
2. To scan using “-v” option.
nmap -v www.geeksforgeeks.org
It is used to get more detailed information about the remote machines.
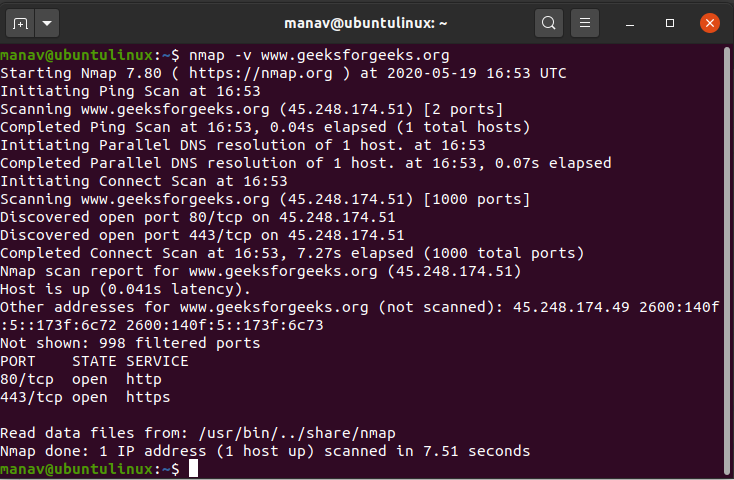
3. To scan multiple hosts
nmap 103.76.228.244 157.240.198.35 172.217.27.174
We can scan multiple hosts by writing IP addresses or hostnames with nmap.
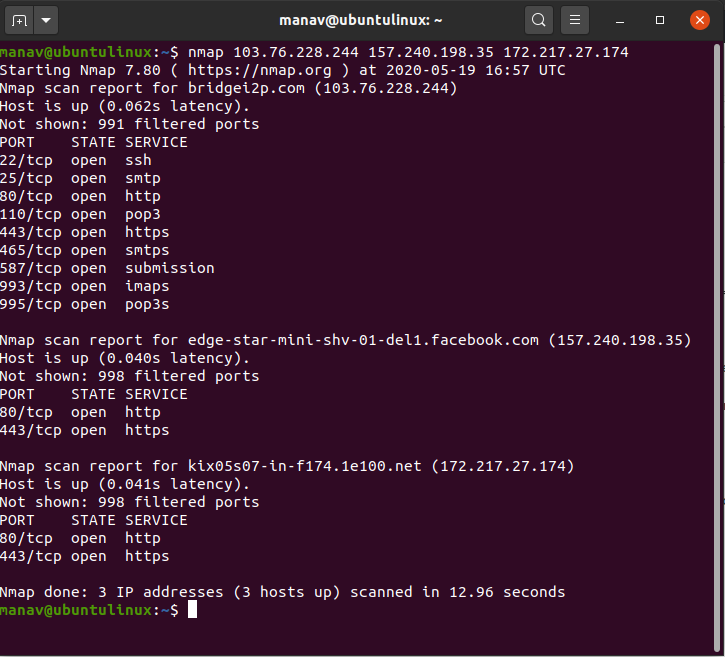
4. To scan whole subnet
nmap 103.76.228.*
We can scan a whole subnet or IP range with nmap by providing “*” with it. It will scan a whole subnet and give the information about those hosts which are Up in the Network.
5. To scan specific range of IP address
nmap 192.168.29.1-20
We can specify the range of IP addresses. This command will scan IP address 192.168.29.1 to 192.168.29.20 .
6. To scan to detect firewall settings.
sudo nmap -sA 103.76.228.244
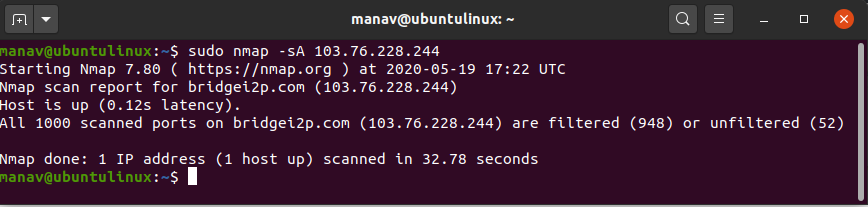
Detecting firewall settings can be useful during penetration testing and vulnerability scans. To detect it we use “-sA” option. This will provide you with information about firewall being active on the host. It uses an ACK scan to receive the information.
7. To identify Hostnames
sudo nmap -sL 103.76.228.244
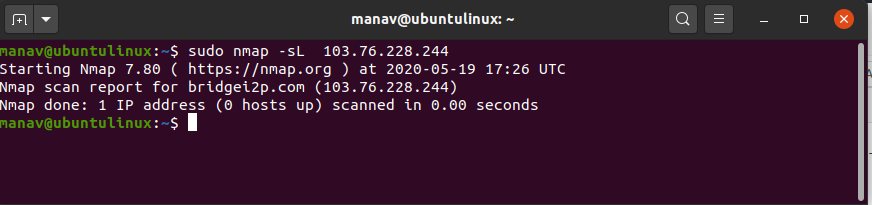
We use “sL” option to find hostnames for the given host by completing a DNS query for each one. In addition to this “-n” command can be used to skip DNS resolution, while the “-R” command can be used to always resolve DNS.
8. To scan from a file
nmap -iL input.txt
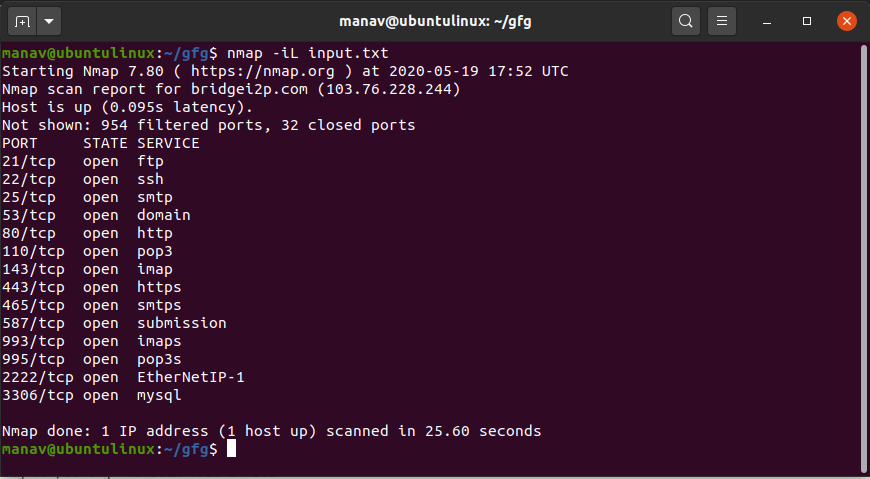
If we have a long list of addresses that we need to scan, we can directly import a file through the command line. It will produce a scan for the given IP addresses.
9. To get some help
nmap -h
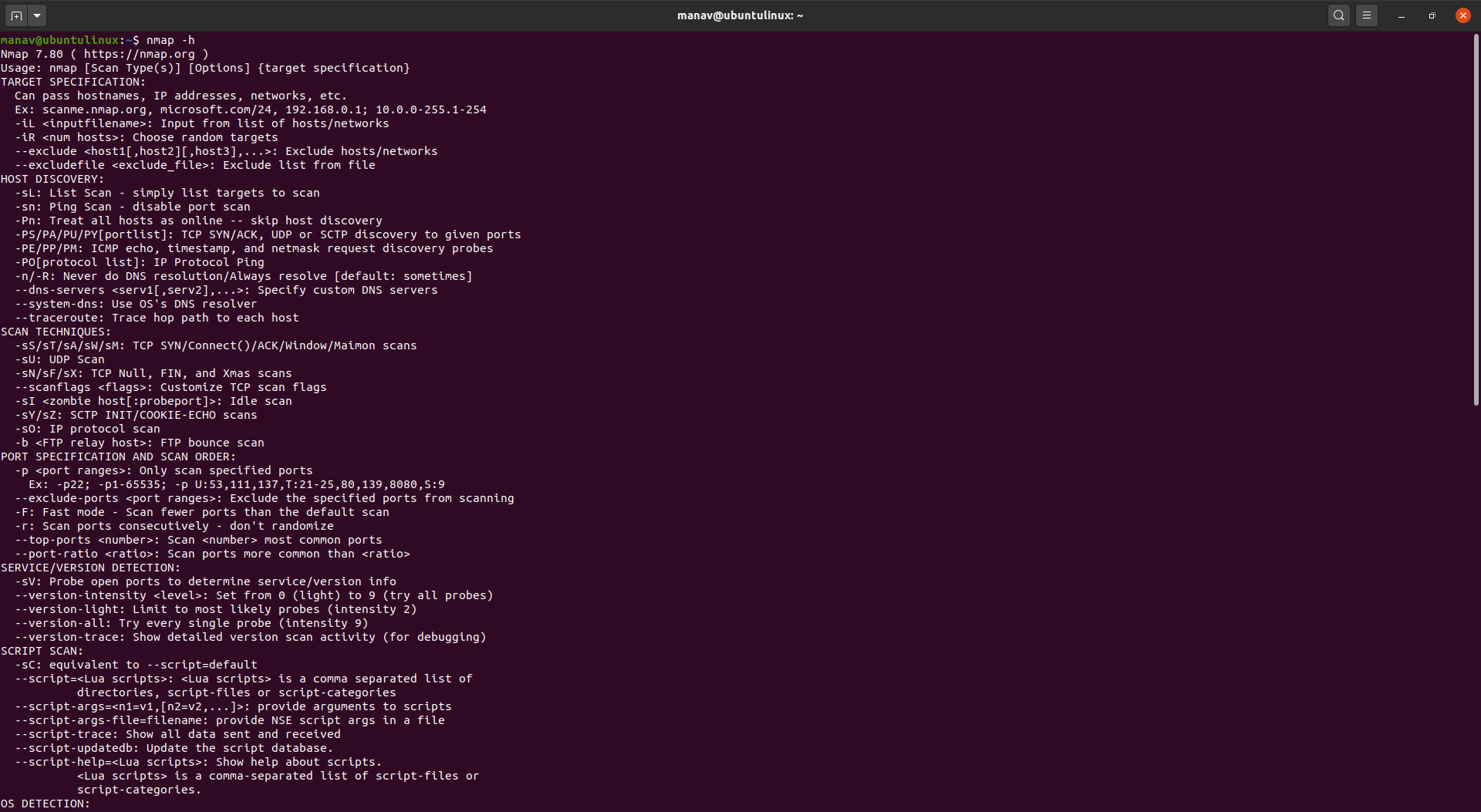
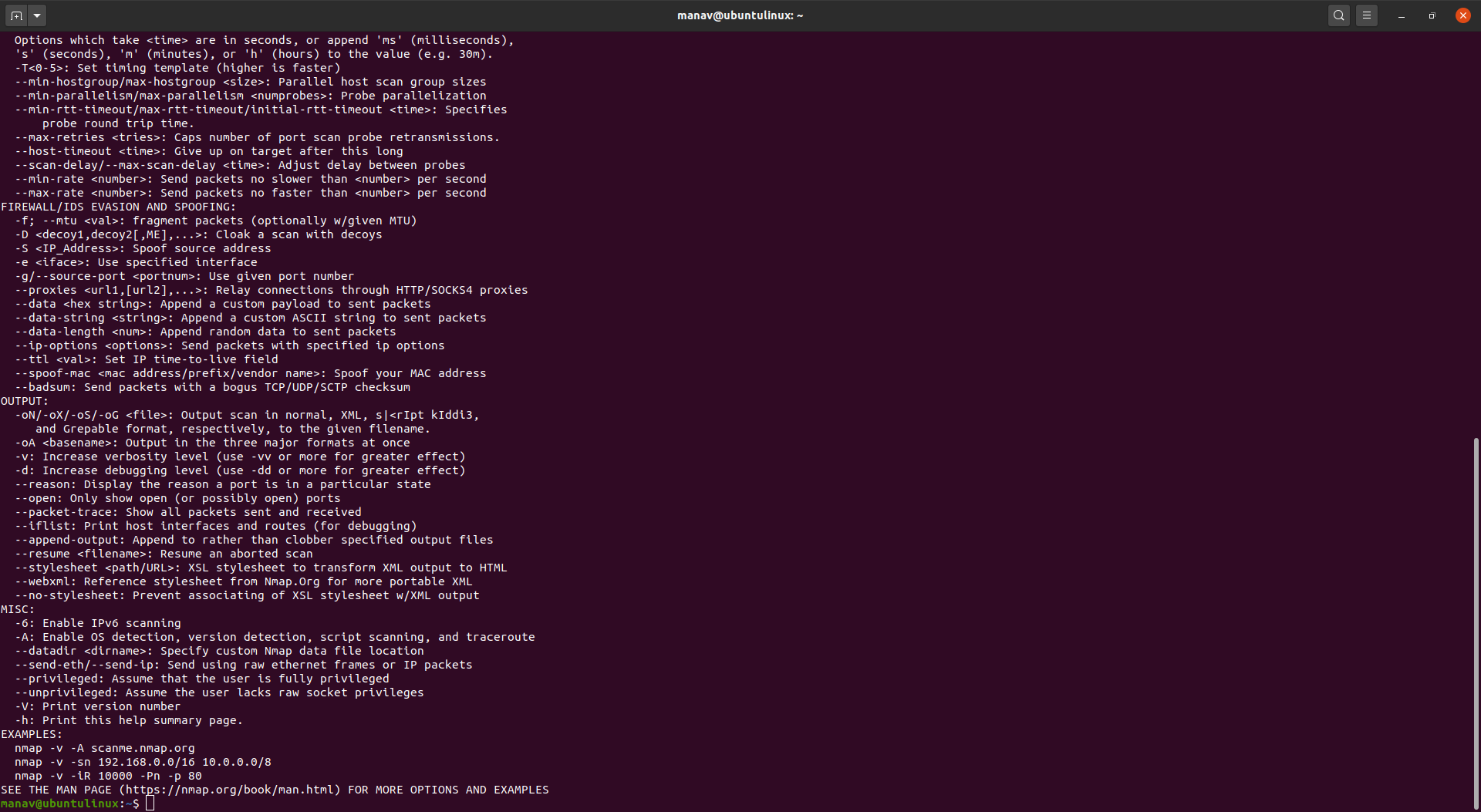
We use the “-h” option if we have any questions about nmap or any of the given commands. It shows the help section for nmap command, including giving information regarding the available flags.
10. Here -sS flag is used for TCP SYN Scan, Which is a stealthy and efficient method of scanning for open ports on a target system.
nmap -sS <Domain Name>
11. Here “-oG” flag can be used to store the nmap result in to specific file.
nmap -sS <Domain Name> -oG <file-path>
12. The “-sU” flag is used with nmap to perform a UDP scan, which allows the user to discover open UDP ports and services on a target system.
nmap -sU <Domain Name>
13. The “-sn” flag is used with nmap to perform a ping scan, which sends ICMP requests to a target host or network to determine hosts is up or not.
nmap -sn <Domain Name>
14. The “-p” flag is used with nmap to perform scan on a specific port or range of ports. ( In our case it will scan port 80,443 and 21 )
nmap -p 80 443 21 <Domain Name>
15. We can also specify the range of ports to scan on a network. ( In this case it will scan all the ports in the range of 1 to 80 )
nmap -p 1-80 <Domain Name>
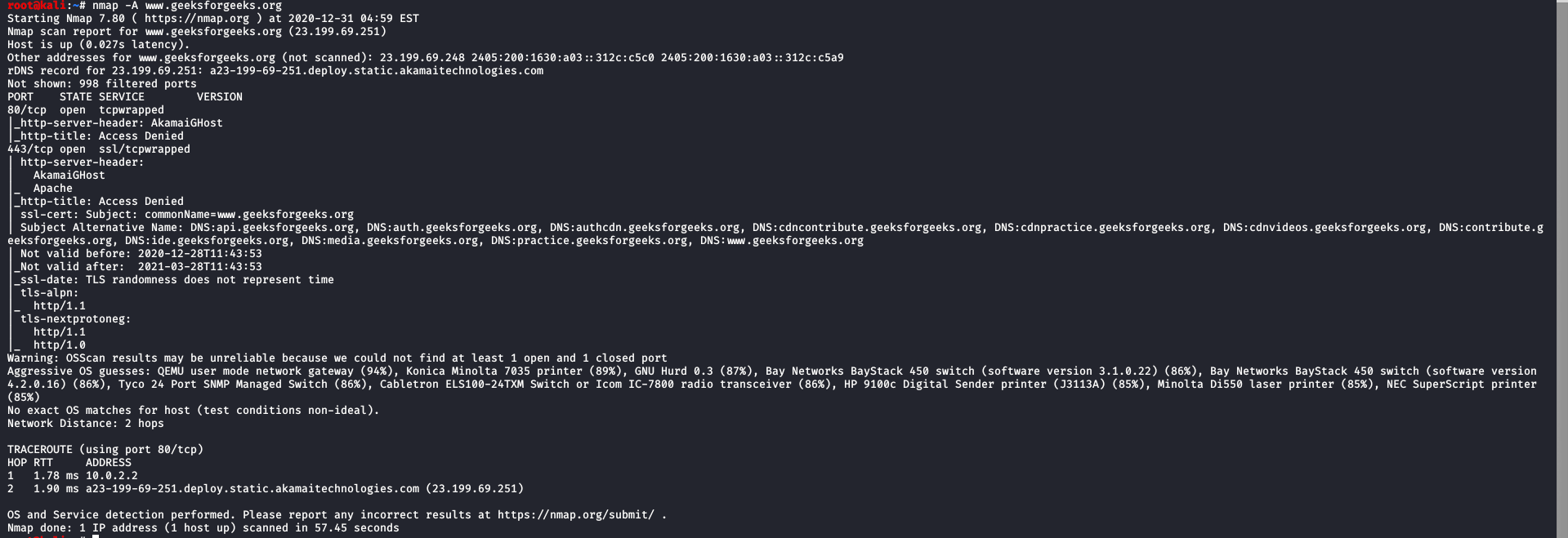
16. Here -A indicates aggressive, it will give us extra information, like OS detection (-O), version detection, script scanning (-sC), and traceroute (–traceroute). It even provides a lot of valuable information about the host.
nmap -A <Domain Name>
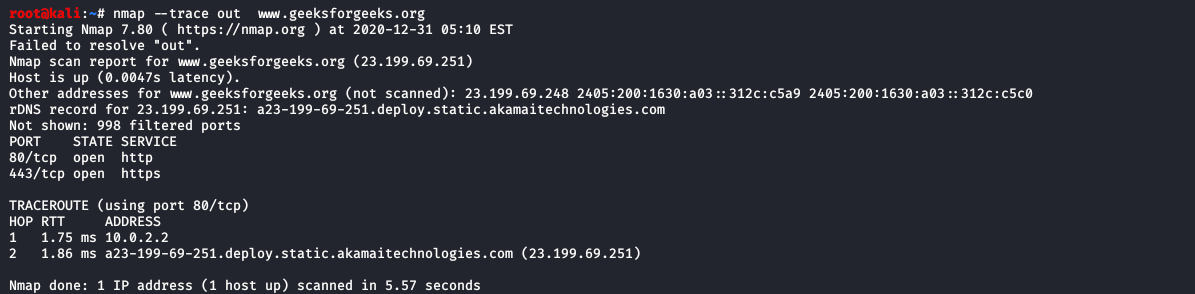
17. Using this command we can discover the target hosting service or identify additional targets according to our needs for quickly tracing the path.
nmap --trace out <Domain Name>
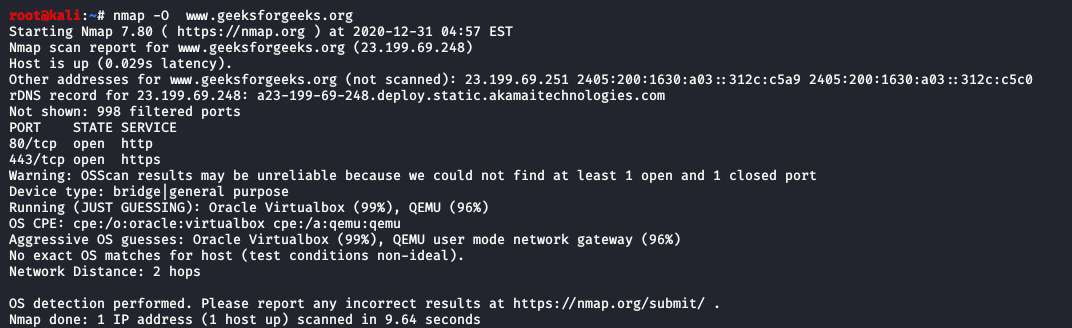
18. Here it will display the operating system where the domain or ip address is running, but will not display the exact operating system available on the computer. It will display only the chance of operating system available in the computer. The command will just guess the running operating system (OS) on the host.
nmap -O <Domain Name>
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...