Legion Tool in Kali Linux
Last Updated :
24 Dec, 2020
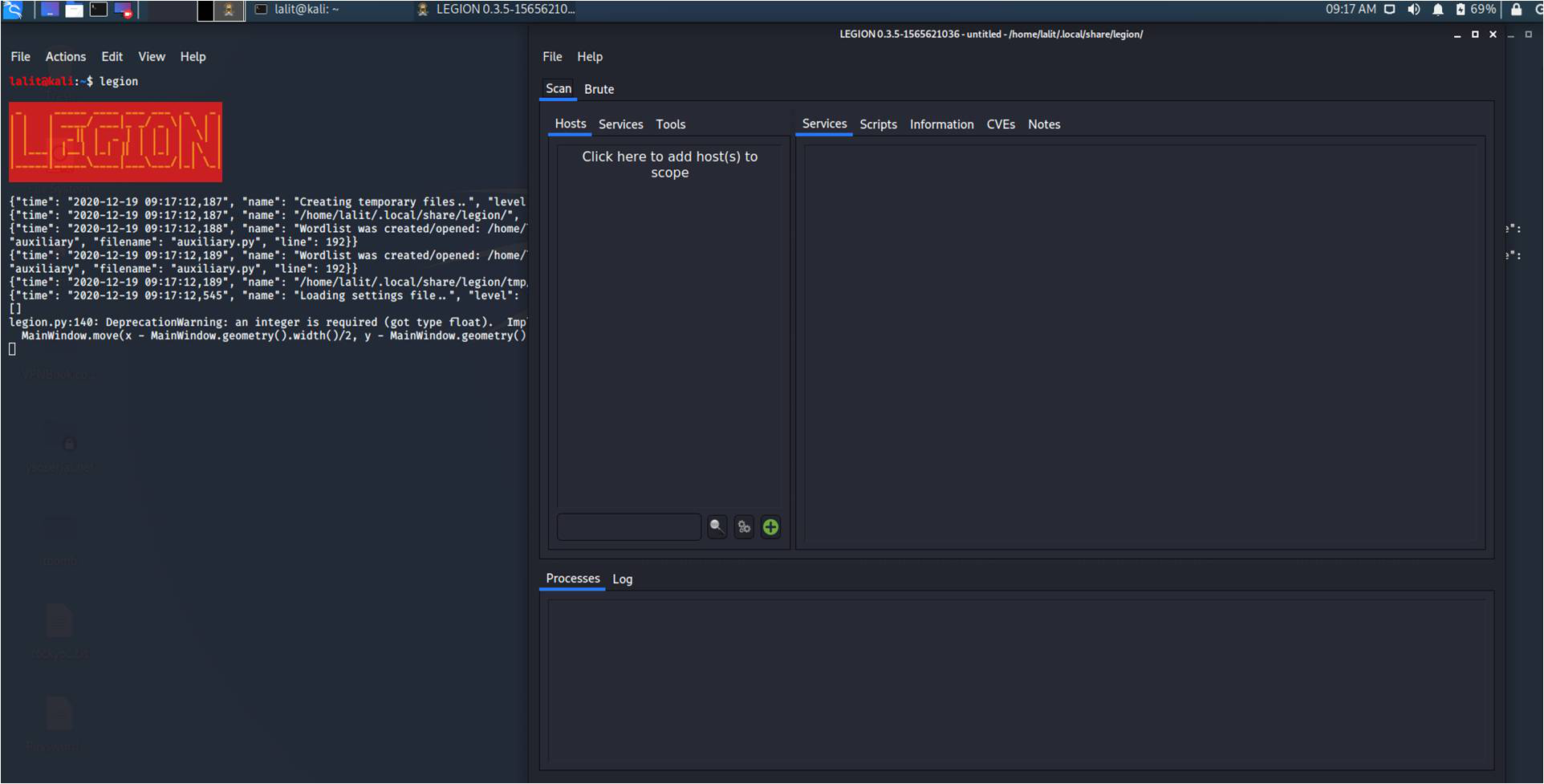
If you are using Kali Linux 2020.1 or up, then instead of Sparta, Kali Linux comes with the Legion, fork version of Sparta with improved features. Legion tool is a super-extensible and semi-automated network penetration testing framework. Legion is very easy to operate.
Features of Legion Tool:
- GUI with panels and a long list of options that allow pentesters to quickly find and exploit attack vectors on hosts.
- It has the feature of real-time auto-saving of project results and tasks.
- Legion also provides services like Automatic recon and scanning with NMAP, whataweb, sslyzer, Vulners, webslayer, SMBenum, dirbuster, nikto, Hydra, and almost 100 auto-scheduled scripts are added to it.
- Modular functionality of Legion Tool allows users to easily customize Legion.
- Automatic detection of CVEs (Common Vulnerabilities and Exposures and CPEs (Common Platform Enumeration).
Notable changes from Sparta tool:
- Legion tool provides estimates of Task completion.
- The elimination of deprecated and unmaintained libraries has been done as Legion is refactored from Python 2.7 to Python 3.6.
- Support for hostname resolution.
- Legion tool revises the processes in queue and execution routines for increased app reliability and performance.
- Legion has a real-time auto-saving of project tasks and results.
- Scanning of vhosts/sni hosts.
- Legion tool is supported by a highly-active development team.
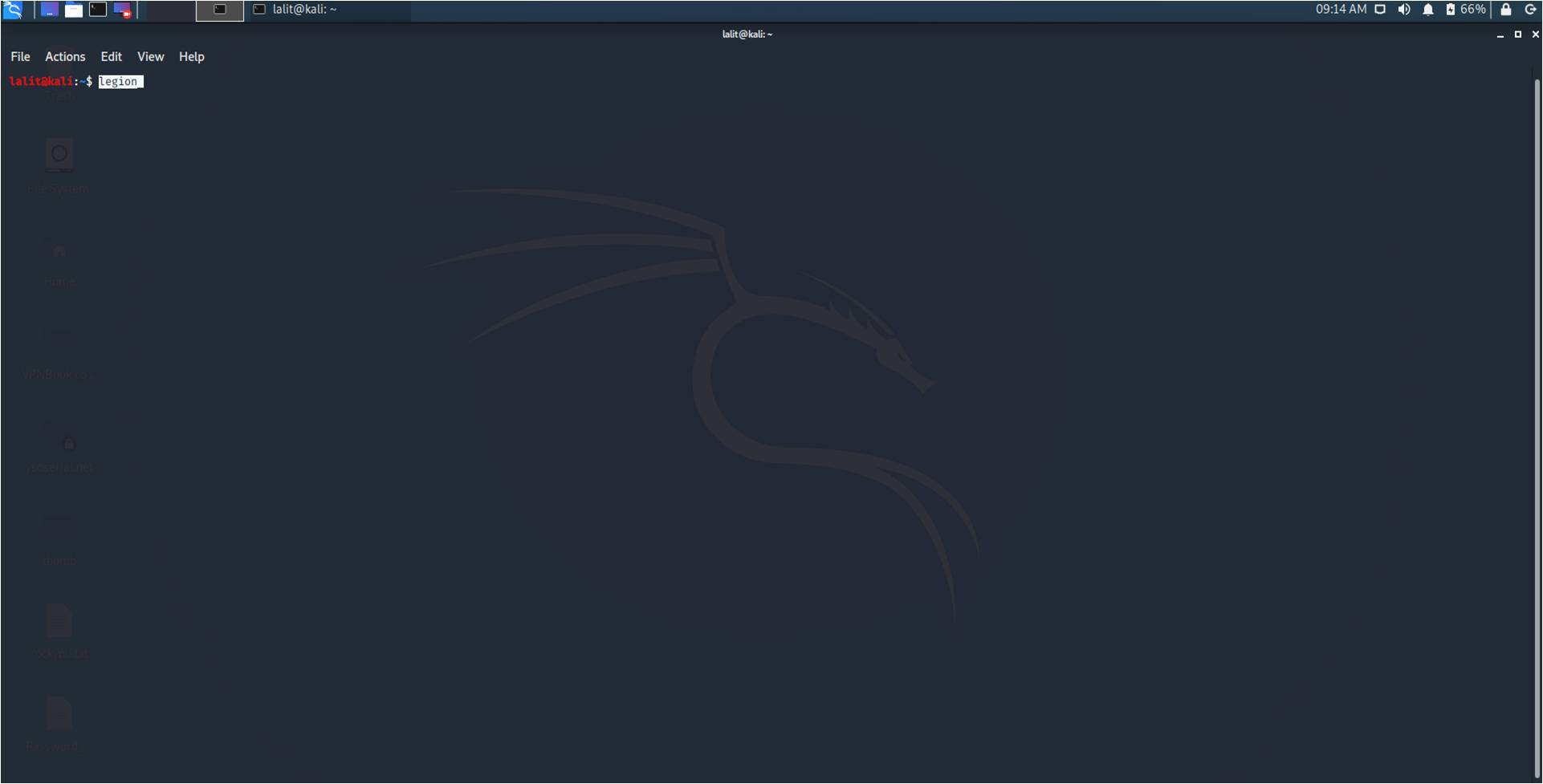
Installation of Legion tool: Usually Legion tool comes pre-installed with Kali Linux but, if we need to install it we can run the following command :
sudo apt-get install legion -y
After the complete execution of the above command, you can start the legion tool from any terminal by simply “legion” command.
legion
In the Hosts section, we have an option to add hosts to the scope. Simply click on add hosts and you will get the below screen :
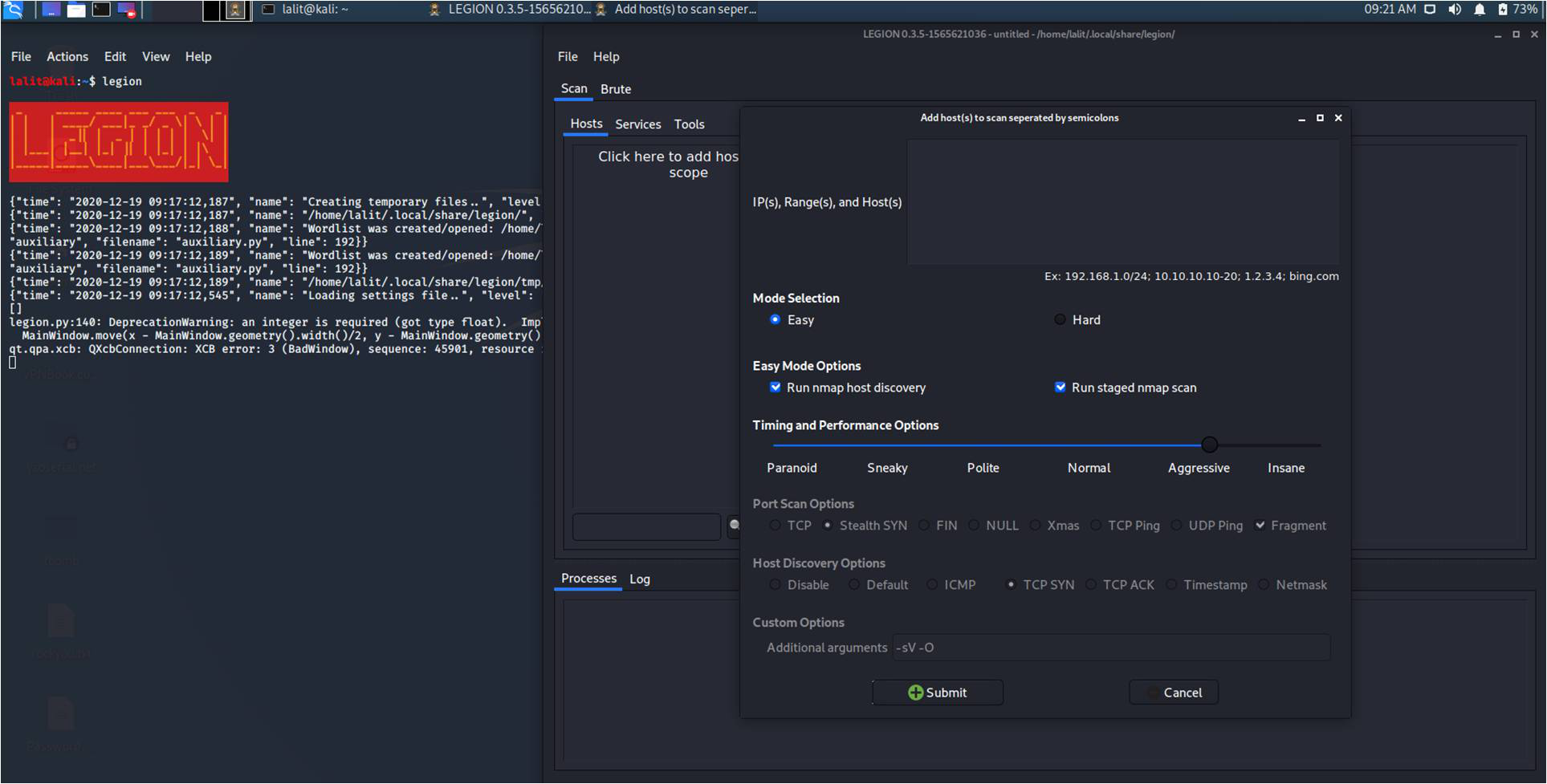
Here we can add a single IP, a range of IPs, or hostnames in the section. In order to add multiple targets simply separate them with a semicolon. Then there is the option for Mode selection, in this section, we have Easy and Hard mode. In Easy mode, we got nmap scanning options like staged scan and nmap host discovery. In Hard mode, we get options like host discovery, custom port scanning, and custom discovery options. In the additional arguments we have -O flag for OS detection and -sV flag for service version.
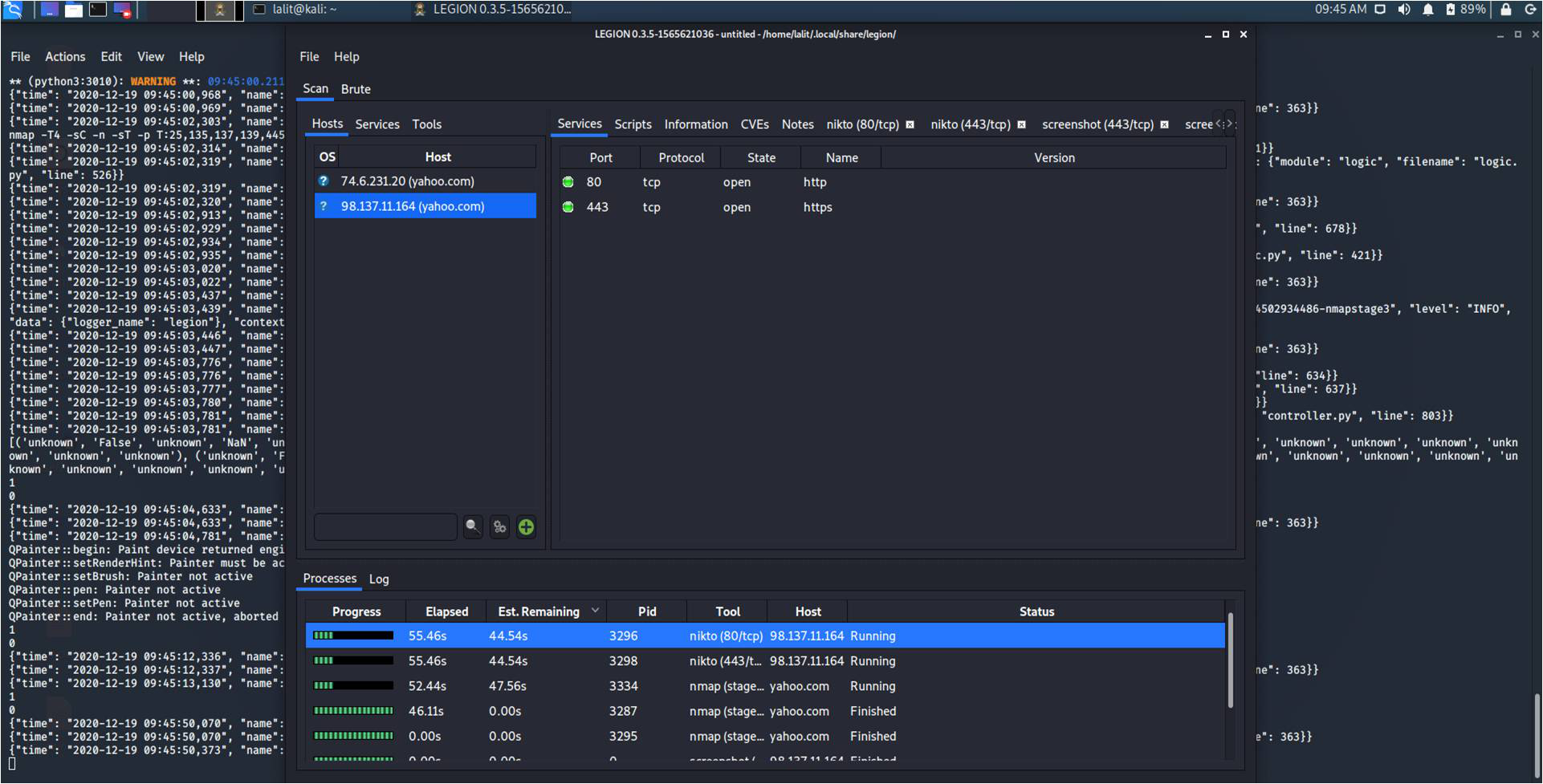
Performing scan with Legion Tool: We are performing an Easy mode scan on yahoo.com with -sV and -O arguments.
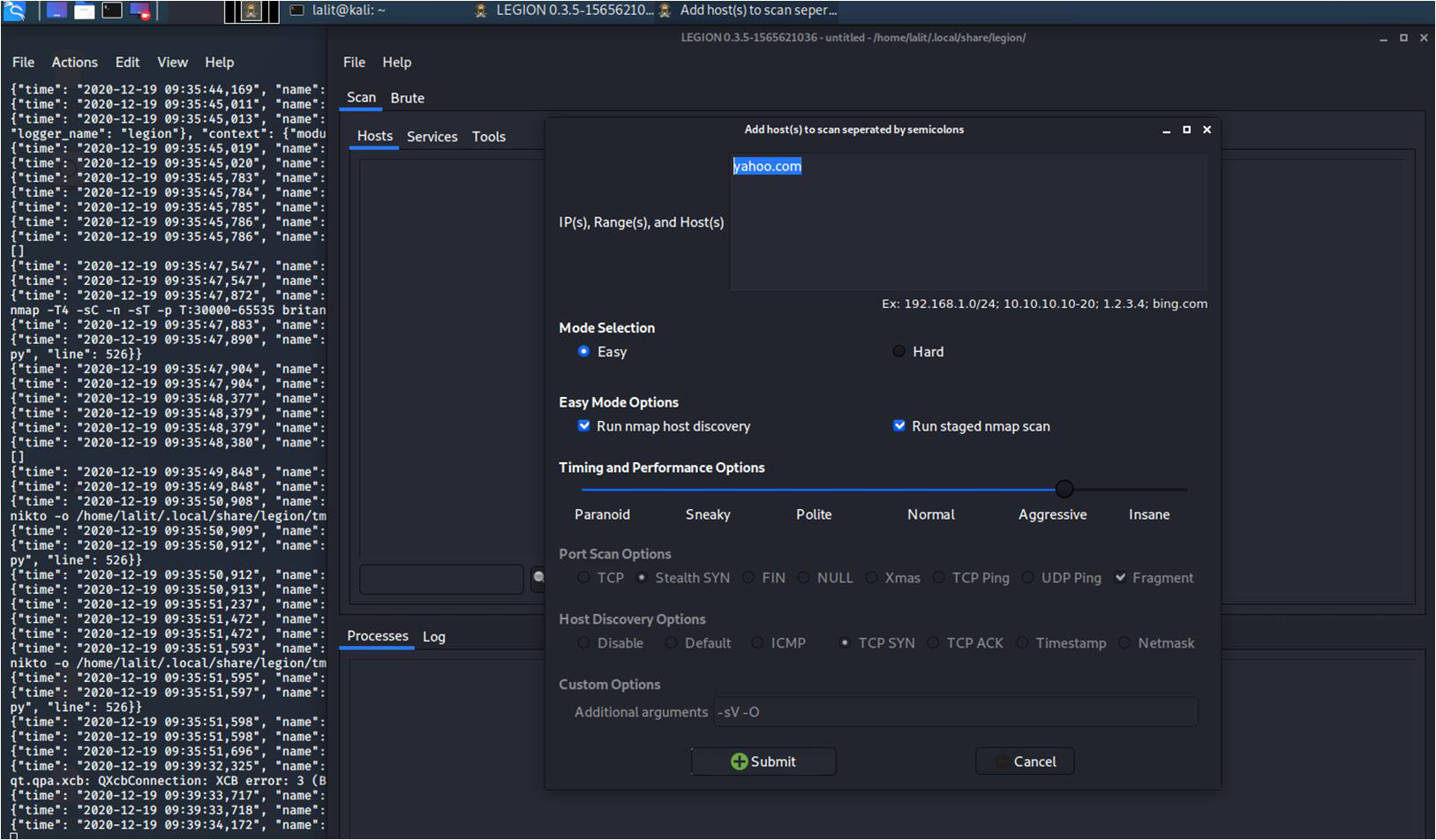
We will get results as shown in the below image.
Share your thoughts in the comments
Please Login to comment...