Kali Linux – Forensics Tools
Last Updated :
28 Jul, 2020
Today when we are surrounded by a lot of ransomware, malware, and digital viruses to spy and invade our policy, there is a great need to learn how to prevent ourselves from them. When it comes to malicious, encrypted, secure, or any other file forensics tools helps us to analyze them and makes our path to the attacker more clear or even sometimes gives us a lot of information about the message in the file or the author of the file. These tools even allow us to encrypt our messages in images or other files to hide it from those who want to read the message because of their malicious intentions. We could analyze or even open the code of any file using the following mentioned tools. Below is the list of the Basic tools for Forensics Tools
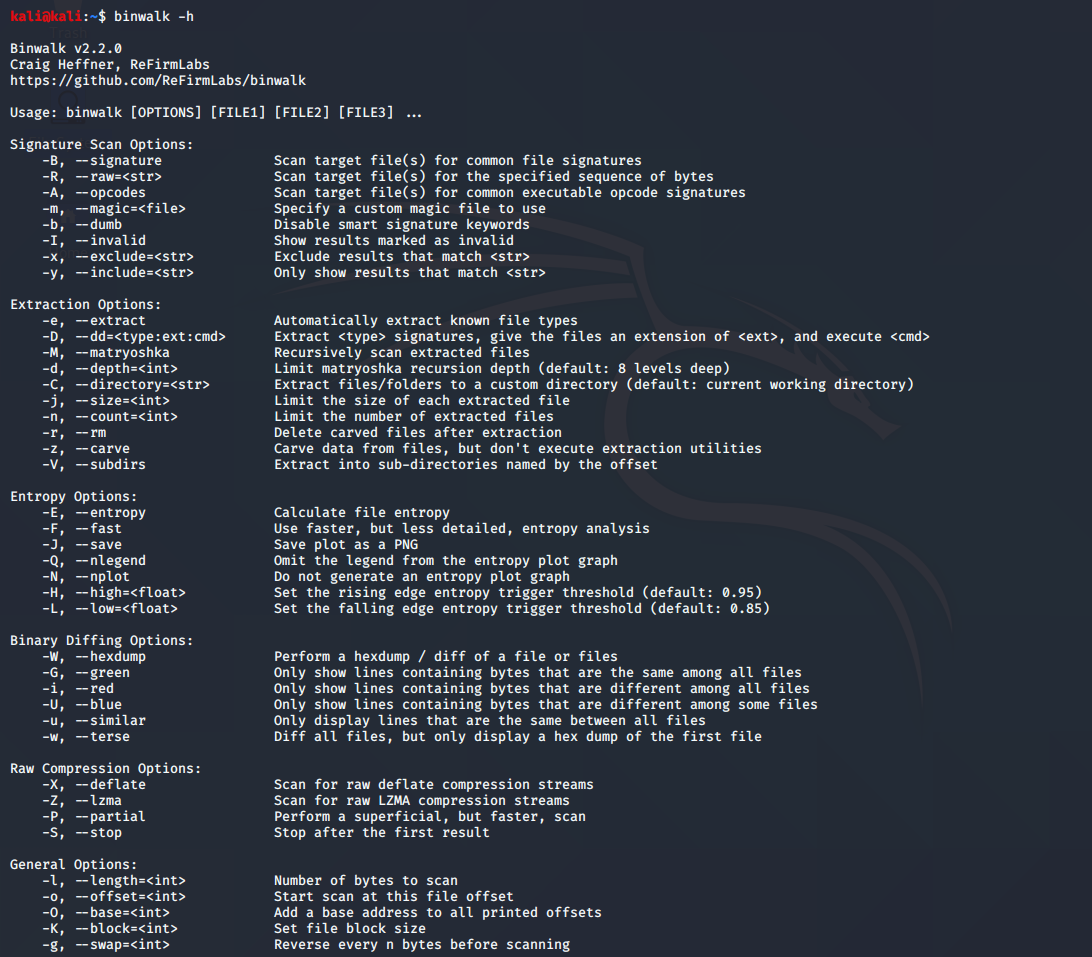
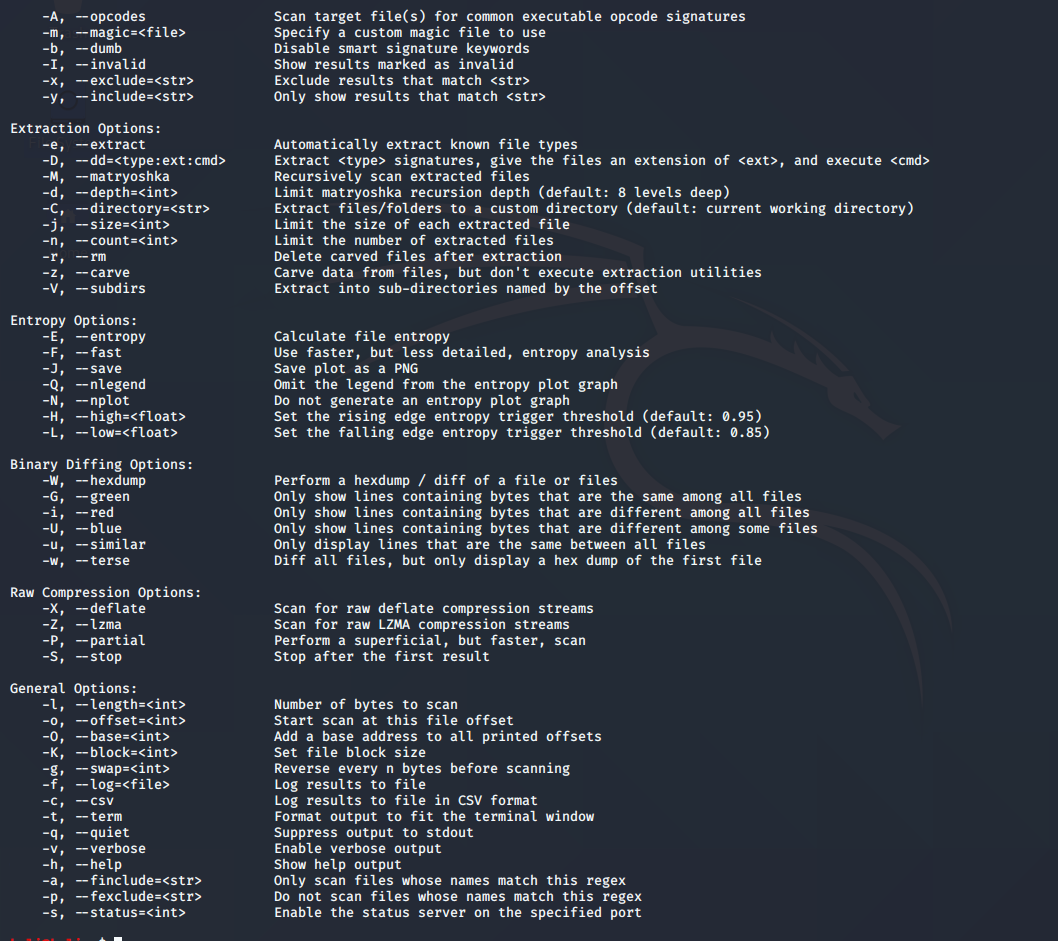
1. Binwalk
Binwalk is a great tool when we have a binary image and have to extract embedded files and executable codes out of them. It is even used to identify the files and codes which are embedded inside the firmware images. Binwalk is compatible with magic signatures for UNIX file utility as it uses libmagic library.
The Official Github Repository for Binwalk is: https://github.com/ReFirmLabs/binwalk
To use Binwalk Tool: Enter the following command in the terminal.
binwalk -h
This will display the help section of the Binwalk command.
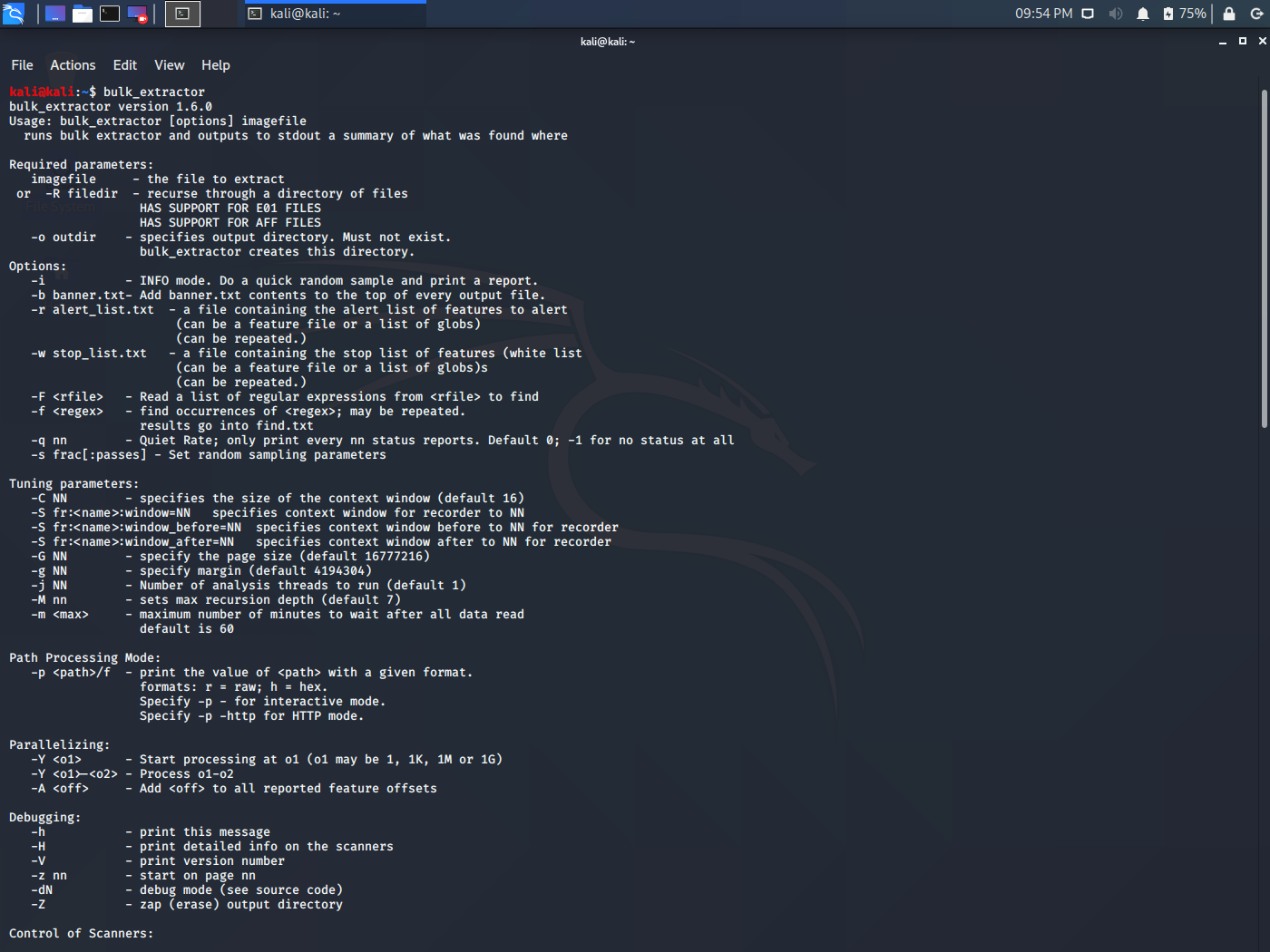
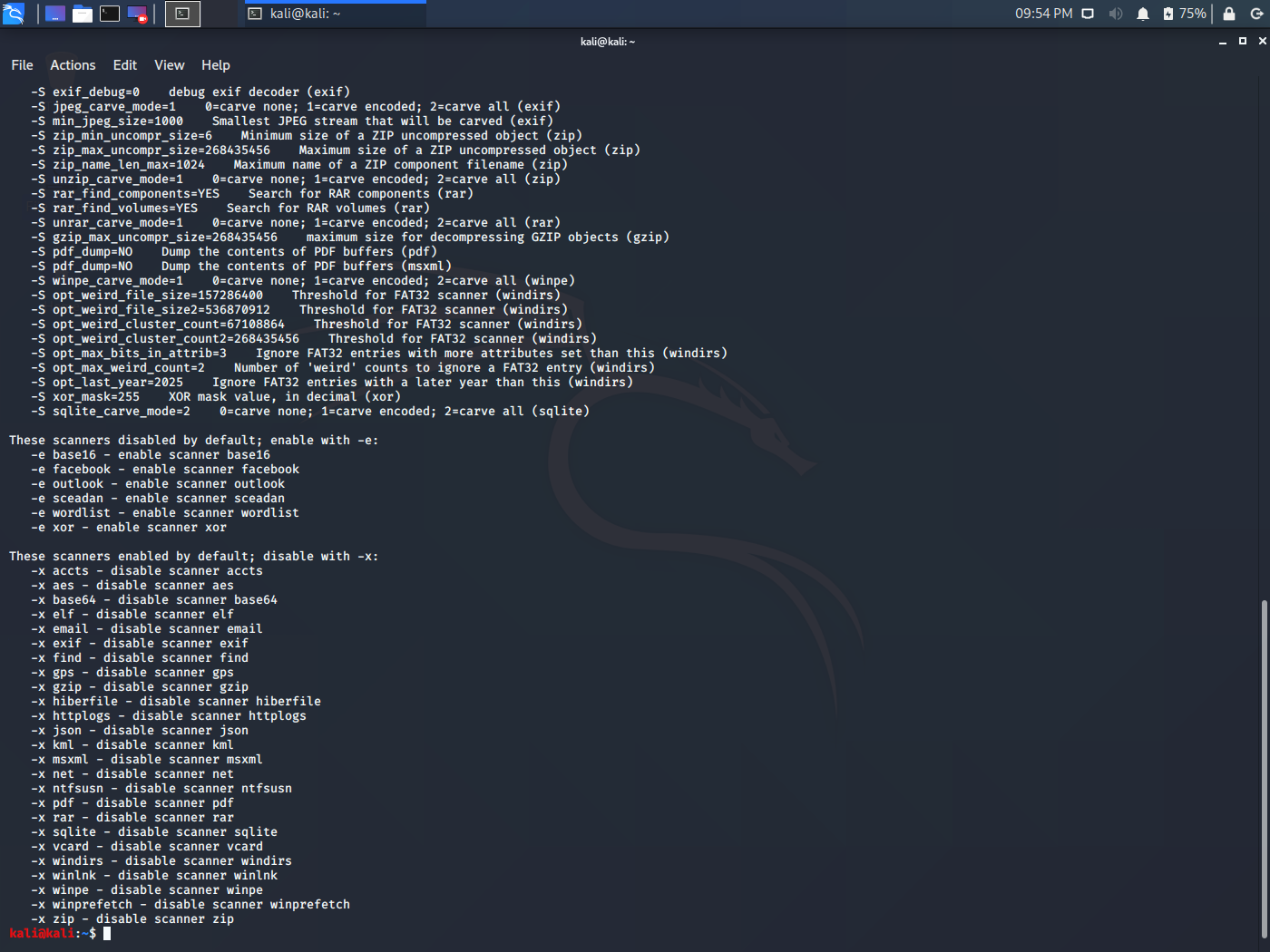
2. Bulk-Extractor
Bulk-Extractor tool which is to be used when you have to extract features like E-Mail address, URLs, Confidential Document Numbers from files. This tool is used for Intrusion investigations, malware investigations, identity investigations, or any other kind of cyber investigation. The awesome feature of working with compressed or corrupt files makes it a great tool to work with those files. IT works on disk images, files, or a directory of files and finds out the useful information.
To use Bulk-Extractor: Enter the following command in the terminal.
bulk_extractor
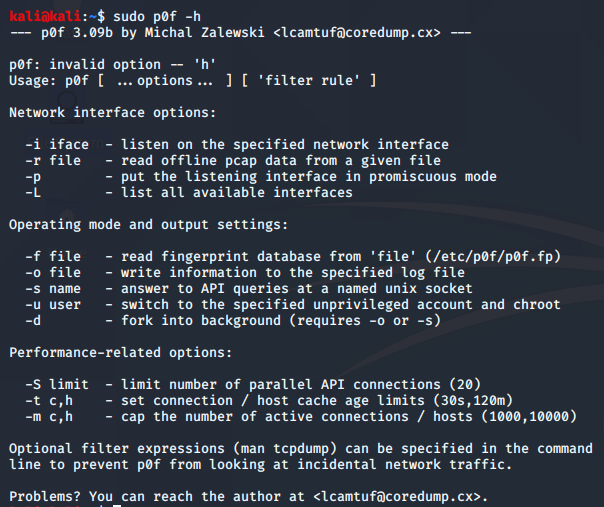
3. p0f
p0f is a great tool when we have to analyze network captured packages. p0f is used to gather the information of the host like the IP address, Operating System, and much more from the package. This tool may prove to be a great tool when there is a firewall over the network of the captured packet. It is very highly scalable and allows the fast identification of host details. It also allows us to perform information gathering while performing vulnerability tests and to monitor the network.
To use p0f: Enter the following command in the terminal.
p0f -h
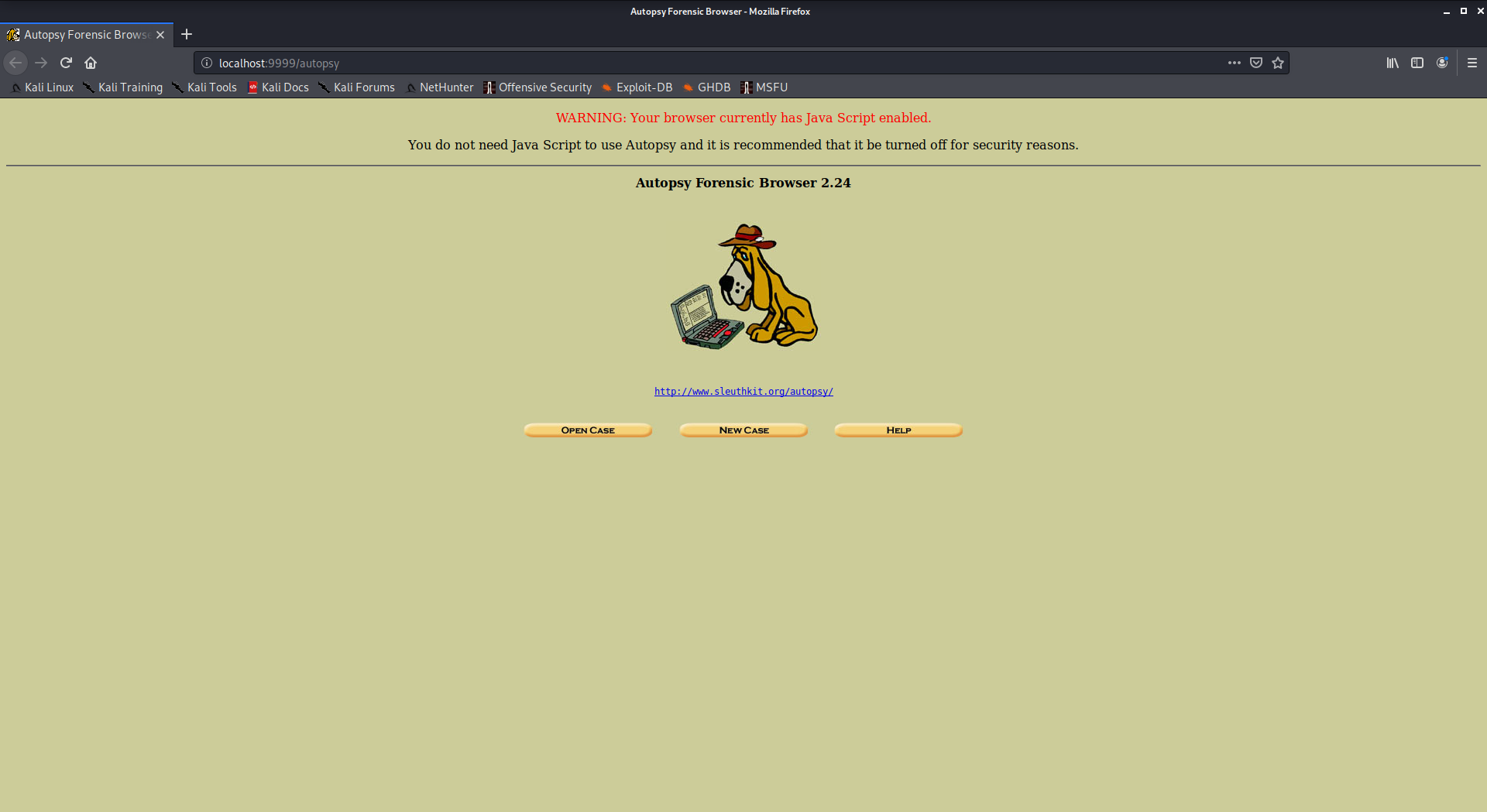
4. Autopsy
Autopsy is a digital forensics tool that is used to gather the information form forensics. Or in other words, this tool is used to investigate files or logs to learn about what exactly was done with the system. It could even be used as a recovery software to recover files from a memory card or a pen drive.
To use autopsy tool
- Autopsy comes pre-installed in Kali Linux
- Just type “autopsy” in the terminal.
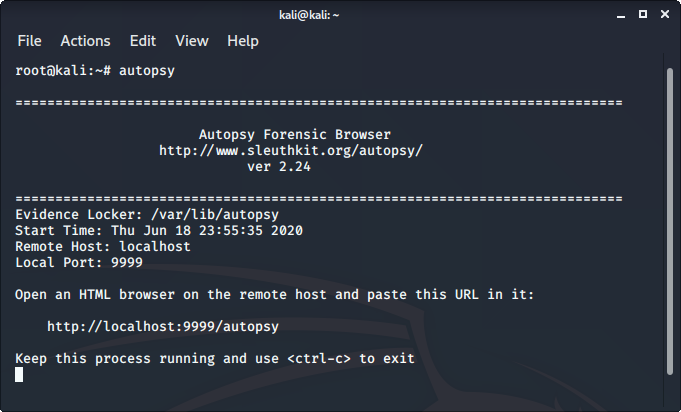
Now visit http://localhost:9999/autopsy in order to use the tool.
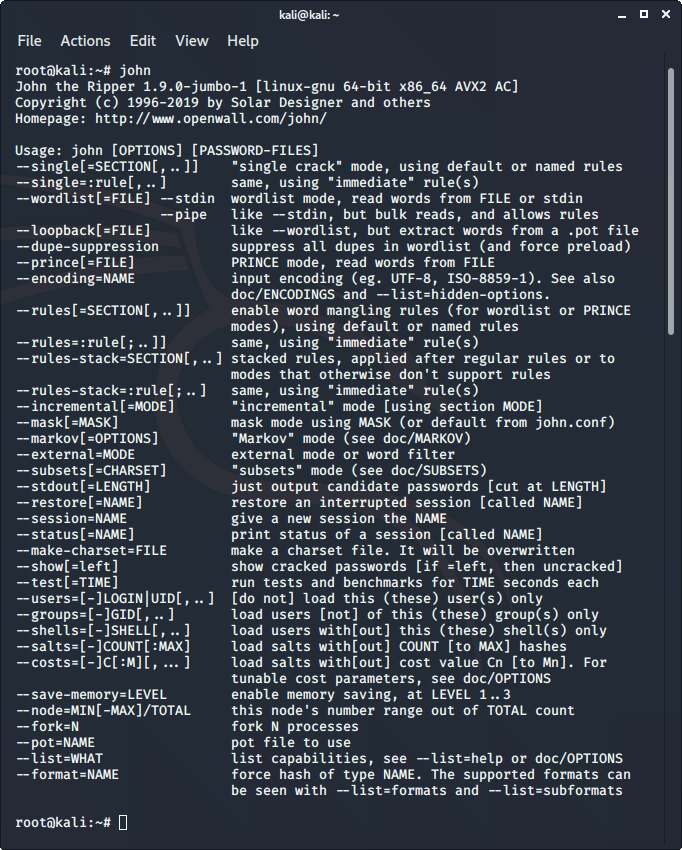
5. John the Ripper
John the Ripper is a great tool for cracking passwords of files like zipped files pdf files etc. These password-protected files can be easily decrypted with john the ripper there are many attacks for the same in it like brute force attack, dictionary attack, etc.
To use John the Ripper
- John the ripper comes pre-installed in Kali Linux.
- Just type “john” in the terminal to use the tool.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...