Kali Linux – Exploitation Tools
Last Updated :
21 Jun, 2022
After Scanning, information Gathering, and finding a vulnerability comes the main concept of hacking which is Exploitation of the vulnerability. Vulnerability is not that effective if it can not be exploited or it could not cause harm to the application, So in order to get the impact of the vulnerability, we have to exploit also in many cases we have to take down a hacker’s or a spammer’s website. So we have to find a vulnerability on the website and have to exploit it. Kali Linux comes packed with 300+ tools for cybersecurity and penetration testing out of which many of the tools are used to exploit these vulnerabilities, a few of them are listed below.
1. Metasploit
Metasploit Framework is basically a penetration testing tool that exploits the website and validates vulnerabilities. This tool contains the basic infrastructure, specific content, and tools necessary for penetration testing and vast security assessment. Metasploit Framework is one of the most famous exploitation frameworks and is updated on a regular basis. It can be accessed in the Kali Whisker Menu and launched directly from the terminal. Also here, new exploits are updated as soon as they are published. It contains many tools that are used for creating security workspaces for vulnerability testing and penetration testing systems. It was designed by rapid7 LLC and is completely open-source software and is easy to use. To use Metasploit:
- Metasploit comes pre-installed with Kali Linux
- Just enter “msfconsole” in the terminal.

2. BeEF
BeEF or Browser Exploitation Framework is basically a penetration testing tool that runs and gets executed on the web browser. It also allows professional penetration testers to use client-side attack vectors to assess the actual security posture of a target environment. This tool mainly focuses on the Web Browser. It hooks web browsers in order to use them as a base or launchpad to attack the system and execute the malicious codes and payloads. To use BeEF, enter the following command in the terminal.
beef-xss

3. Armitage
Armitage is a tool that is used to visualize targets, recommend exploits, and expose exploitation features in the framework. Armitage is basically a scriptable red team collaboration tool for the Metasploit framework in other words it is a GUI version of the Metasploit framework. It contains many tools that are used for creating security workspaces for vulnerability testing and penetration testing systems. Being a GUI-based package, it is a good alternative to Metasploit. To use Armitage, enter the following command in the terminal.
armitage

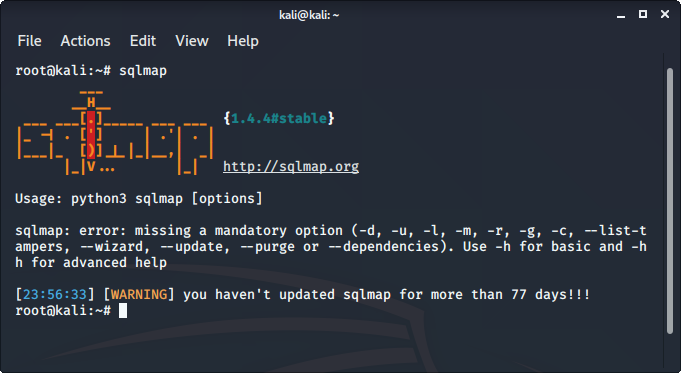
SQLMap is an open-source tool that is used to automate the process of manual SQL injection over a parameter on a website. It detects and exploits the SQL injection parameters itself all we have to do is to provide it with an appropriate request or URL. It supports 34 databases including MySQL, Oracle, PostgreSQL, etc. To use sqlmap tool:
- sqlmap comes pre-installed in Kali Linux
- Just type sqlmap in the terminal to use the tool.
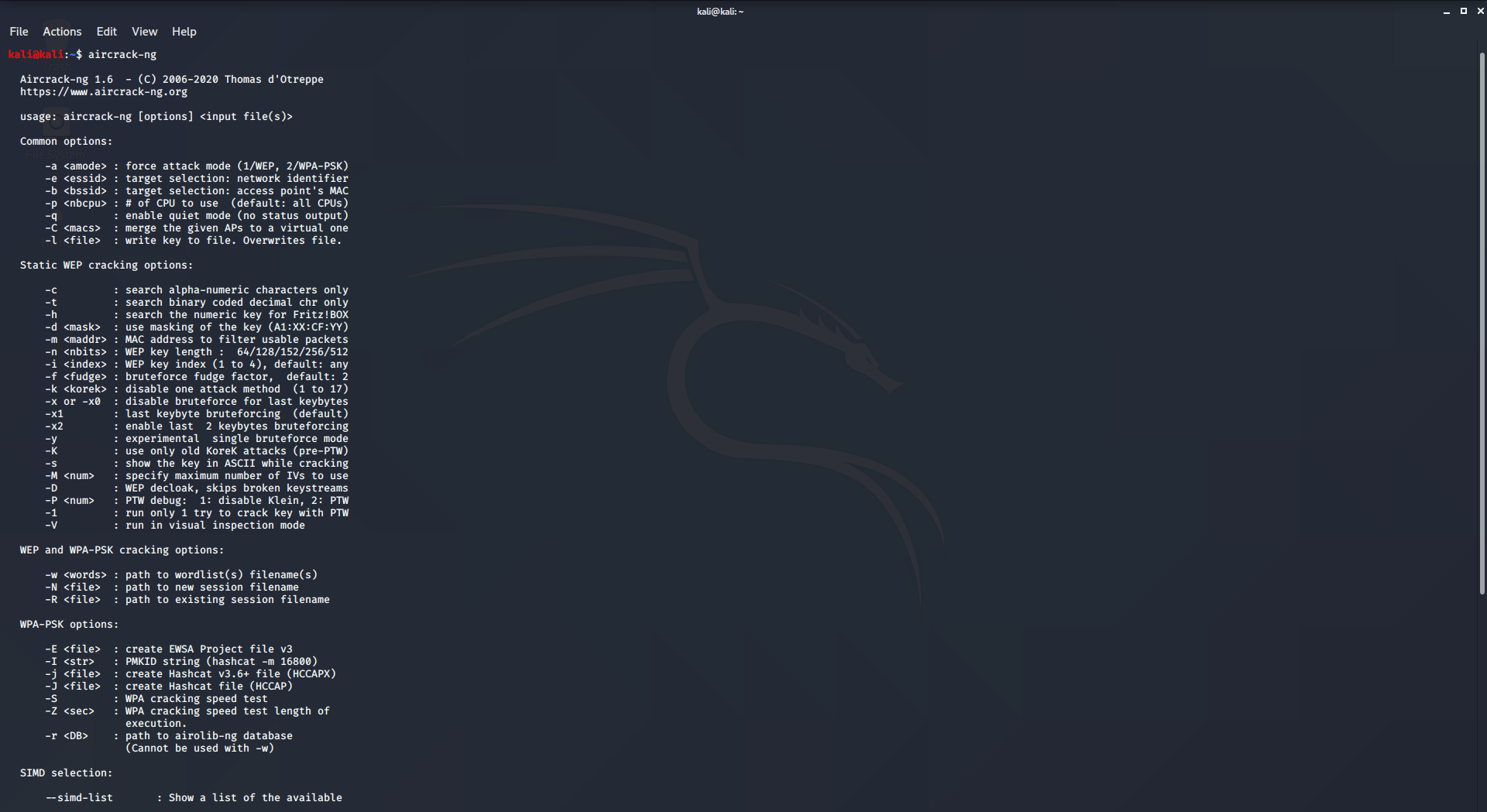
5. aircrack-ng
Aircrack is an all-in-one packet sniffer, WEP and WPA/WPA2 cracker, analyzing tool, and a hash capturing tool. It is a tool used for wifi hacking. It helps in capturing the package and reading the hashes out of them and even cracking those hashes by various attacks like dictionary attacks. It supports almost all the latest wireless interfaces. To use aircrack-ng, enter the following command in the terminal:
aircrack-ng
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...