How to Generate a Self-Signed Certificate with OpenSSL in Linux?
Last Updated :
27 Feb, 2020
TLS (Transport Layer Security) is a secured protocol which is currently in trend. It can see used on top of the HTTP and application layer. The primary use of this protocol is to set up secure communication between web applications and servers. TLS protocol can also be used for secure email transfer, messaging and voice over IP.
Why SSL/TLS secure certificate?
Everyone wants a save website and secured payment gateways so that any kind of username, password and one-time password can not be used by a third party. SSL is a secure way of surfing the internet and it is used to protect our sensitive data. SSL/TLS is required to protect your websites.
Use of SSL/TLS secure certificate
We can use SSL/TLS secure certificate to establish an encrypted way of communication between you and the only recipient that you want to convey a message. We need a secure network packets so that it can not be accessed by third party. Here comes the role of the SSL/TLS secure certificate who can provide us the proper authentications while transferring network packets.
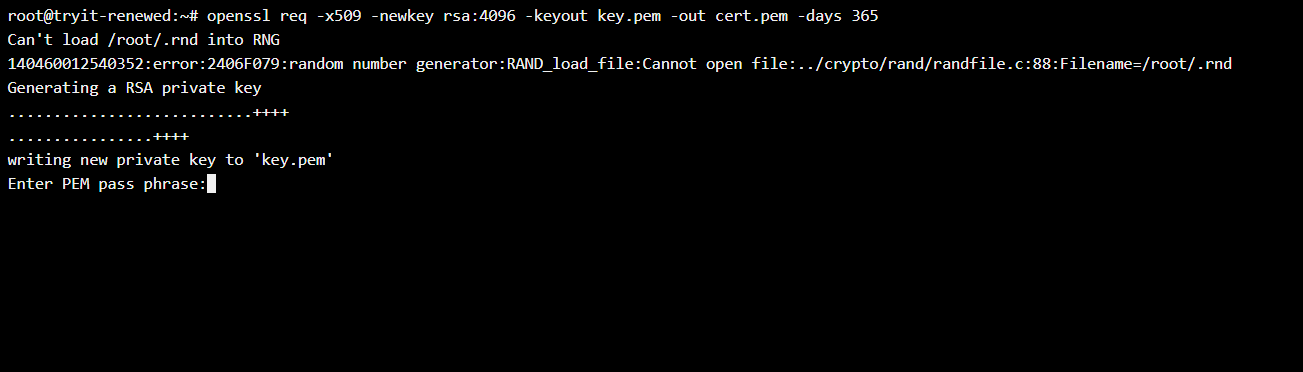
With the help of below command, we can generate our SSL certificate
openssl req -x509 -newkey rsa:4096 -keyout key.pem -out cert.pem -days 365
This certificate is valid only for 365 days. Most of the parameters are fixed in this command like req, keyout and out. The private key name is up to your choice but it is required and the same for certificate as well. Below are the following steps that have to be followed to create this certificate.
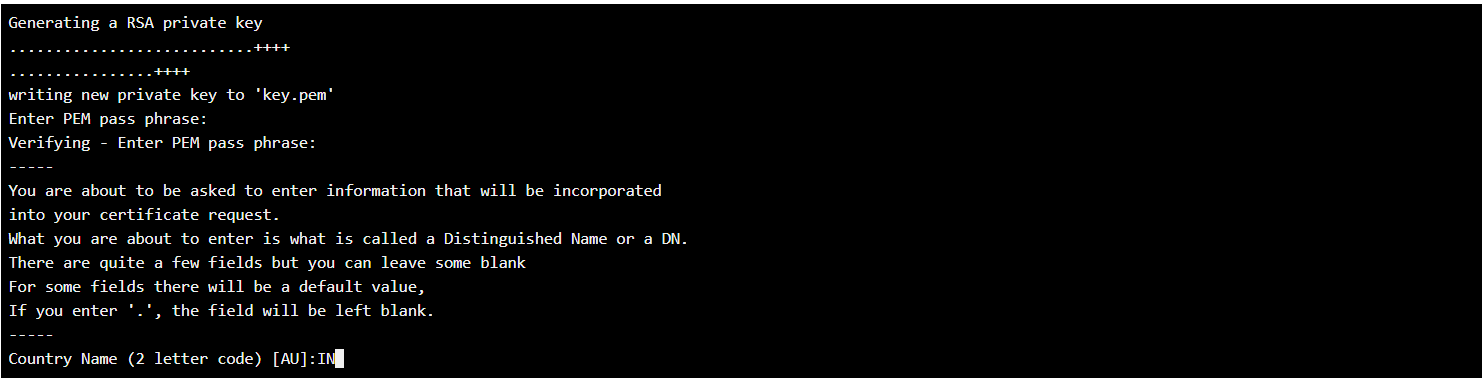
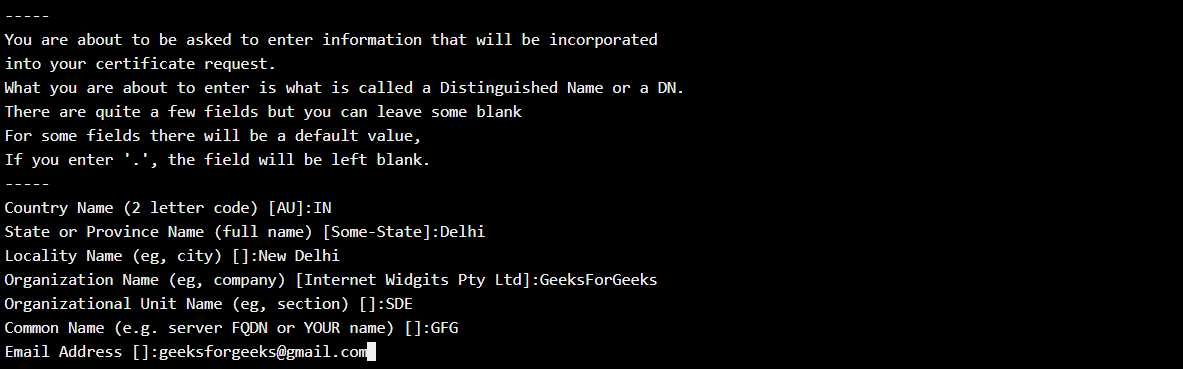
Step 1: In this step, one should provide a password that is always required when you set up a connection with your server. One will not able to see the password while writing the password.
Step 2: In this step, one has to provide the country name with the starting two letters of your country.
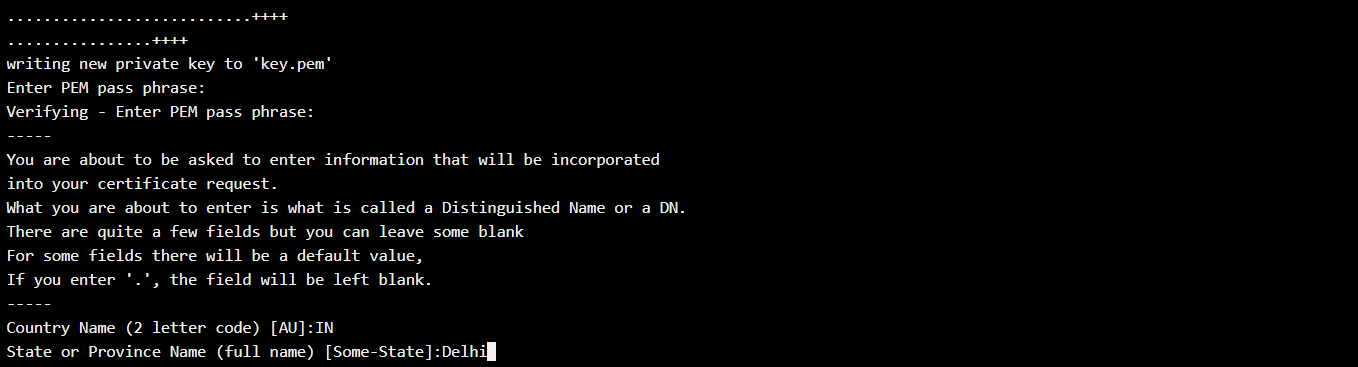
Step 3: In this step one has to provide the full name of the state.
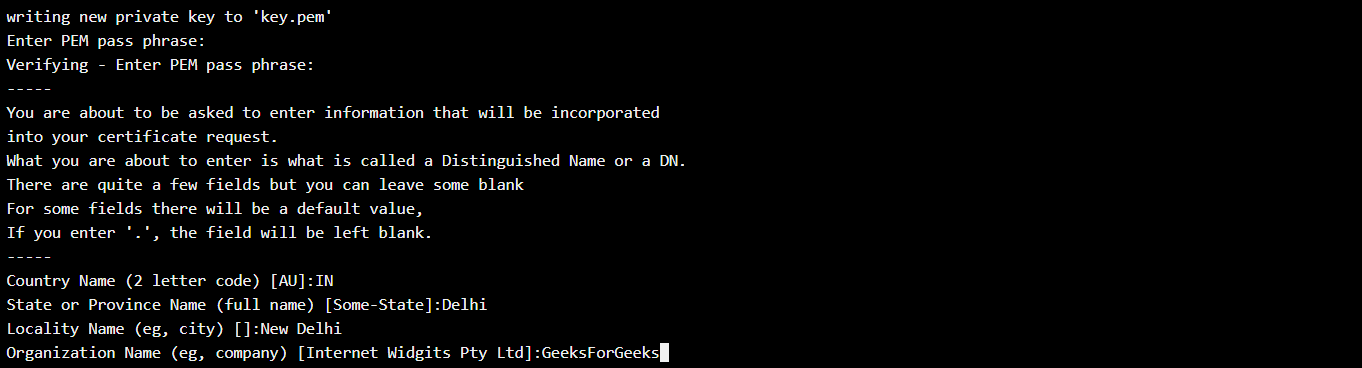
Step 4: In this step, one has to provide the organization name in which you are working or an organization for which this certificate is used for.
Step 5: In this step one has to provide the email address of your organization or if you are working as an individual one can give your email address.
After all the above steps are to be followed to make an SSL certificate and private key.
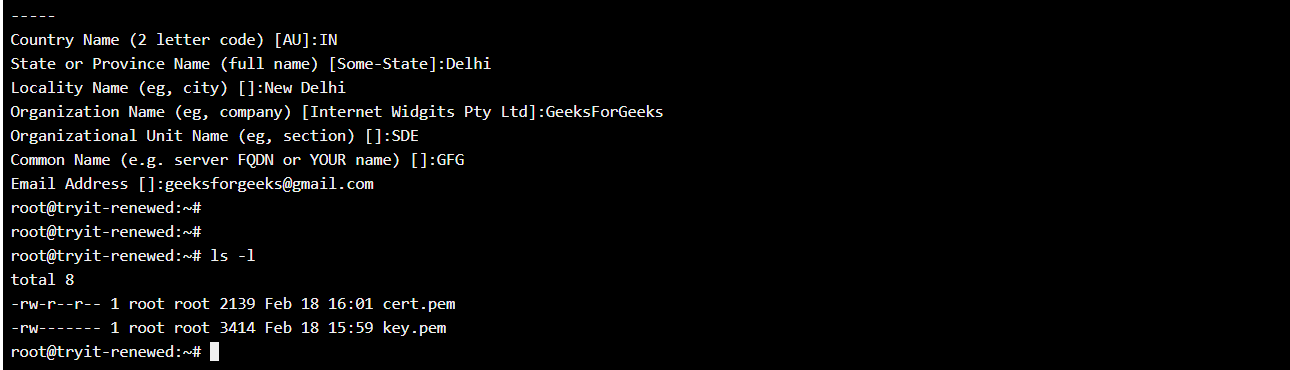
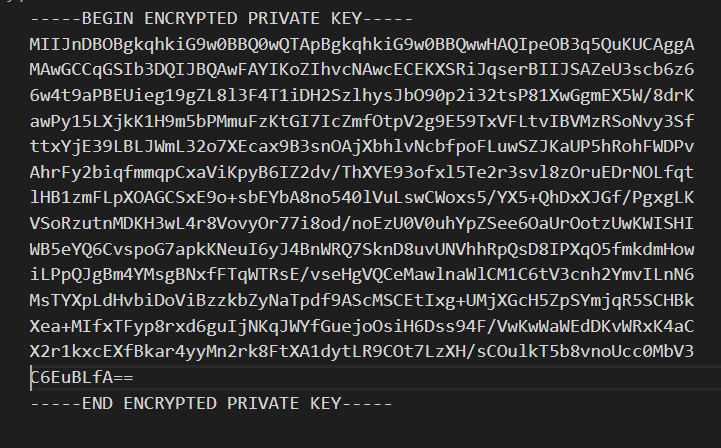
Private Key Generated:
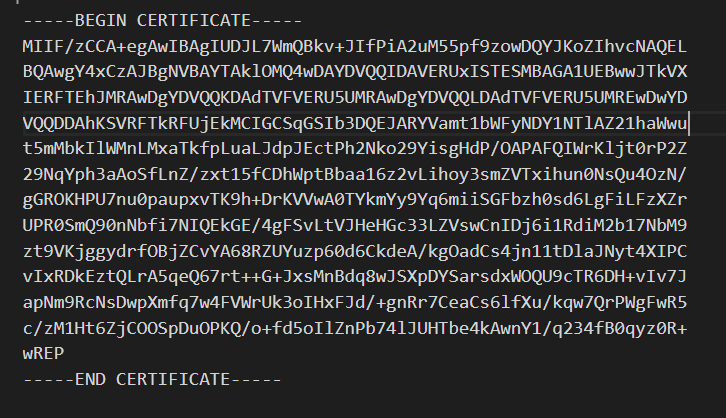
SSL Certificate Generated:
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...