History of Cryptography
Last Updated :
06 Oct, 2022
Humans have two basic needs when we take about communication. One is the need to communicate selectively, to communicate and share information. These two basic needs while communicating gave rise to coding and encrypting the messages in such a way that only intended people could have access to the information.
The word ‘cryptography’ originated from two greek words ‘Krypto’ means hidden and ‘graphene’ means writing.
Classical Cryptography
The roots are cryptography are found in Roman and Egyptian civilizations. Below are some of the ancient types of cryptography:
1. Hieroglyphs Cryptography: The earliest known use of Cryptography can be dated back to 1900 BCE during the time of the Old Kingdom of Egypt in form of non-standard hieroglyphs.
- Hieroglyphs were a secret form of communication that the Egyptians used to communicate with one another.
- This secret text was known only to the scribes of the kings who used to transmit messages on their behalf.
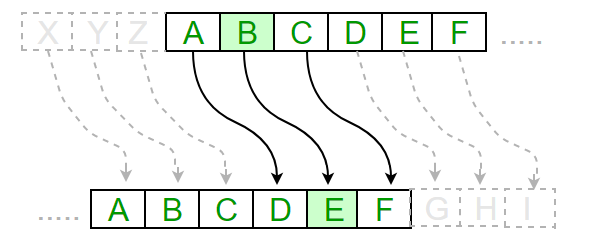
2. Caesar Cipher: The ancient Greeks were well known for the use of Ciphers. The Caesar Cipher or Shift Cipher is one of the earliest and simplest well-known cryptographic techniques. It is a form of Substitution Cipher where each character in a word is replaced by a fixed number of positions. For example with a shift of 3, A is replaced by D, B by E, and so on.
3. Vigenere Cipher: During the 16th century, Vigenere designed a cipher in which the encryption key is repeated multiple times spanning the entire message, and then the cipher text is generated by adding the message character with key character modulo 26. This approach is also vulnerable to attacks, where the secrecy of the message depends on the secrecy of the encryption key.
4. Hebern rotating machine: At the start of the 19th century, Hebern designed a Hebern rotating machine. In this machine, a single rotor is used where the secret key is embedded in the rotating disc and the key has an embedded substitution table. Each key press from the keyboard resulted in the output of cipher text. This code is broken by using the letter frequencies.
5. Enigma machine: Cryptography played a vital in the victory of Allied forces during World War I and World War II. World War II prominently saw the use of electromechanical cipher machines. The story of the Allied victory over the Germans by cracking the world-famous Enigma machine is well known. Like all rotor machines, Enigma is a combination of electro-mechanical subsystems. It consisted of somewhat three to five rotors. Whenever a key was pressed, one or more rotors rotated on the spindle, and accordingly, the key was scrambled to something else. The Enigma cipher was broken by Poland.
Data Encryption Standard (DES)
In the early 1970s, IBM realized that its customer base is requesting some type of encryption method to protect the data. They formed a crypto group headed by Horst-Feistel. This group designed a cipher called Lucifer. In 1973, the Nation Bureau of Standards (NBS) which is now known as the National Institute of Standards and Technology (NIST) put out a proposal for the block cipher. Lucifer was eventually accepted and called Data Encryption Standard (DES).
- It is a symmetric-key algorithm based on the Feistel cipher and is used for the encryption of electronic data.
- It has a relatively small key size of 56-bits and is encrypted 64 bits or 8 characters at a time.
- In 1997, DES was broken by an exhaustive search attack.
- But, it was later discontinued as it was found to be insecure, especially against brute force attacks cause of its relatively small key size.
Advance Encryption Standard (AES)
In 1997, NIST again put out a proposal for a new block cipher. The Rijndael cipher is eventually accepted and renamed as Advanced Encryption Standard (AES).
- DES was replaced by Advance Encryption Standard or AES in 2001.
- Unlike DES, AES is based on a substitution-permutation network.
- AES is a sub-set of Rijndael.
- It is a family of ciphers with different key and block sizes.
- In the case of AES, the block size is 128 bits or 16 characters which means 16 characters can be encrypted at a time.
- It comes with three different key size variants: 128 bits, 192 bits, and 256 bits.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...