Gitem – Github organization reconnaissance tool
Last Updated :
23 Sep, 2021
Gitem is a command-line tool that can help organizations and security professionals find sensitive information remaining in openly available files on GitHub. Gitem tool is developed in the Python language, it is open-source and free-to-use. The tool will repeat over all public organization and member repositories and peer filenames against a range of patterns for files that typically contain delicate or critical information. Looking for delicate data in GitHub repositories isn’t a replacement thing, it’s been known for a short time that things like private keys and credentials are often found with GitHub’s search functionality, however, Gitem makes it easier to sharpen the work on a particular organization
Note: Make Sure You have Python Installed on your System, as this is a python-based tool. Click to check the Installation process: Python Installation Steps on Linux
Installation of Gitem Tool on Kali Linux OS
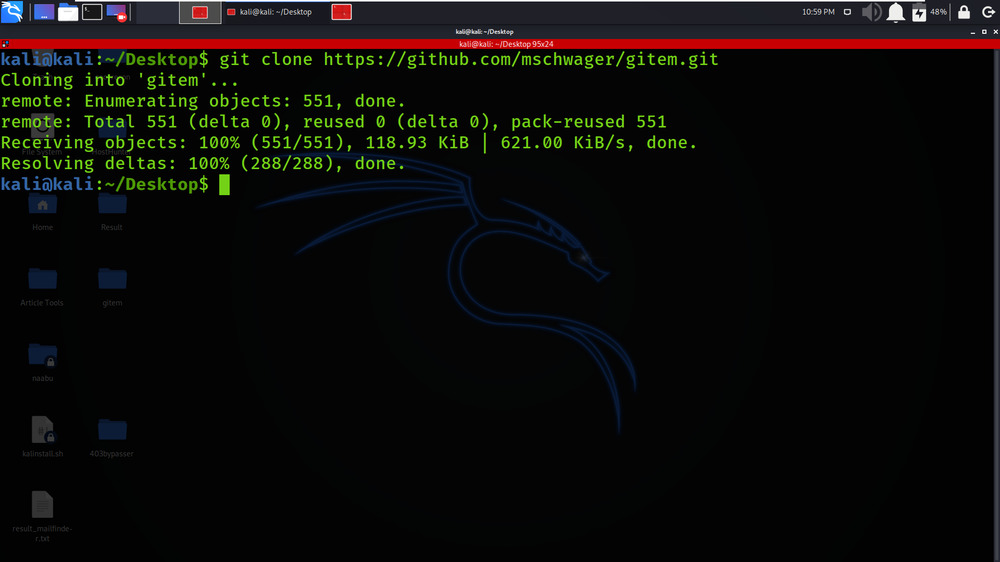
Step 1: Use the following command to install the tool in your Kali Linux operating system.
git clone https://github.com/mschwager/gitem.git
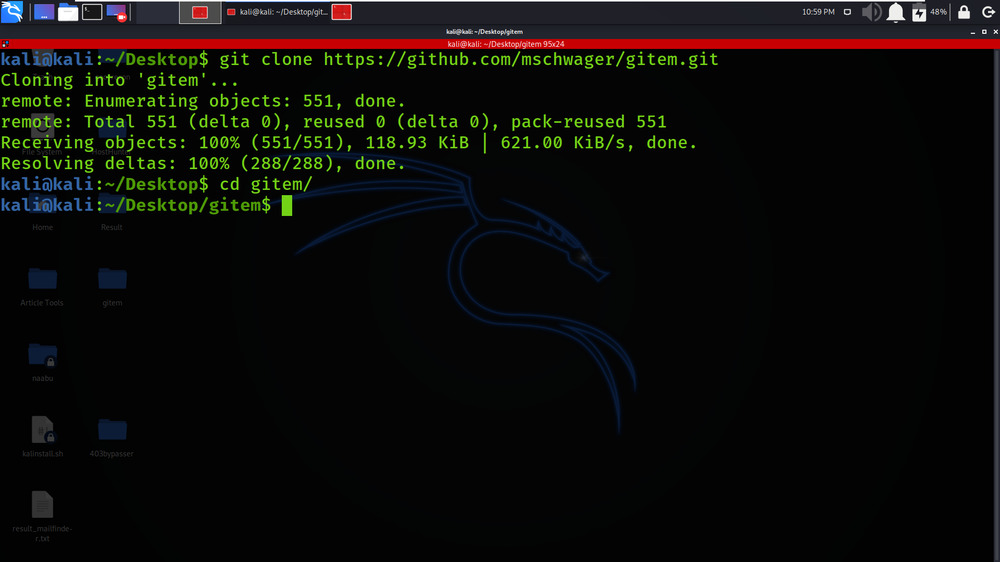
Step 2: Now use the following command to move into the directory of the tool. You have to move in the directory in order to run the tool.
cd gitem
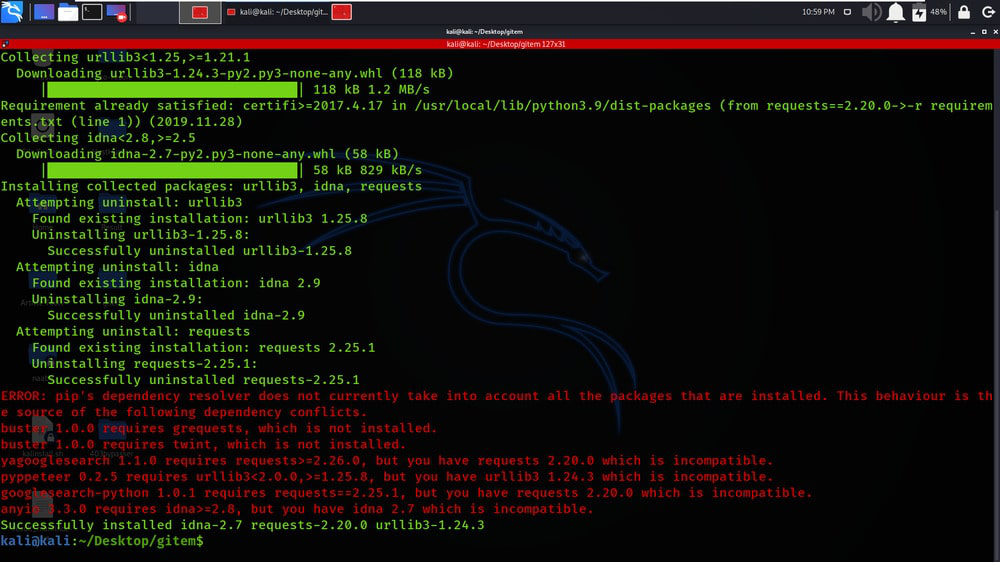
Step 3: You are in the directory of the Gitem. Now you have to install a dependency of the Gitem using the following command.
sudo pip3 install -r requirements.txt
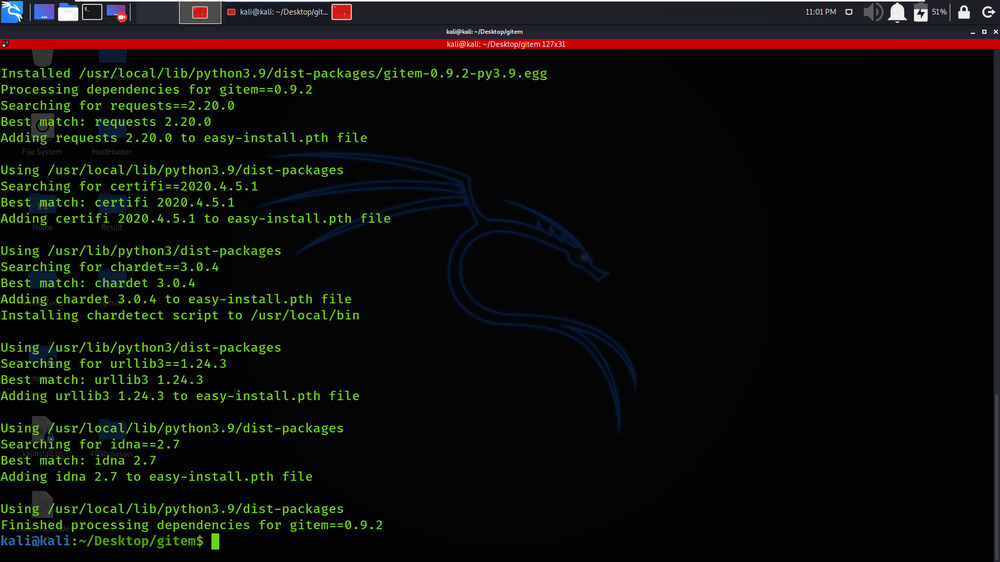
Step 4: Run the setup.py file to complete the installation.
sudo python3 setup.py install
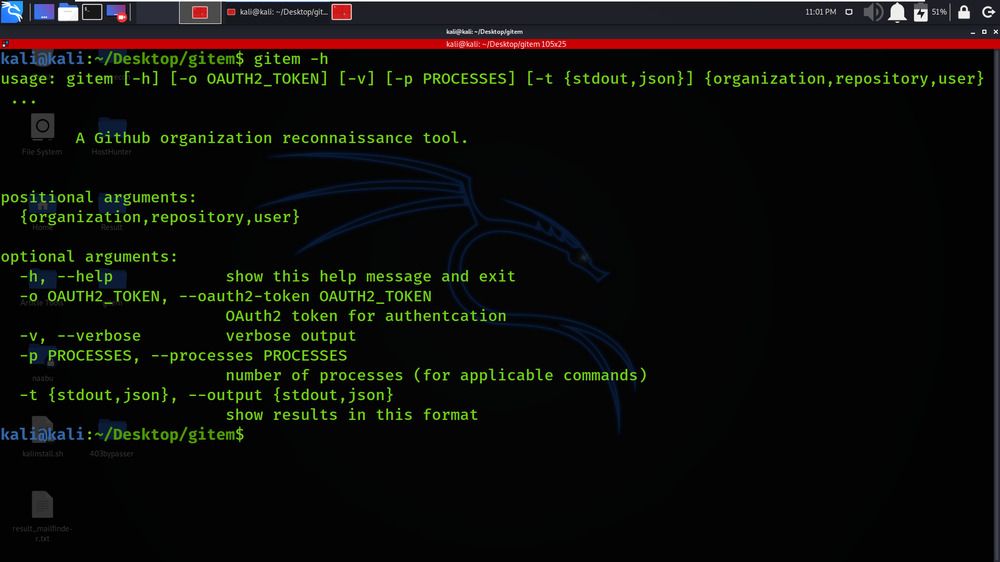
Step 5: All the dependencies have been installed in your Kali Linux operating system. Now use the following command to run the tool and check the help section.
gitem -h
Working with Gitem Tool on Kali Linux OS
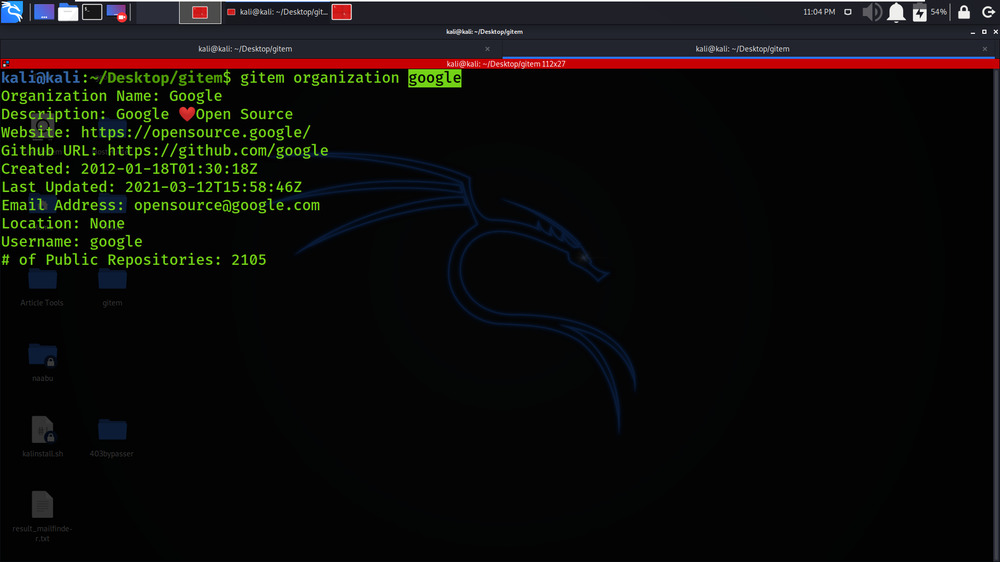
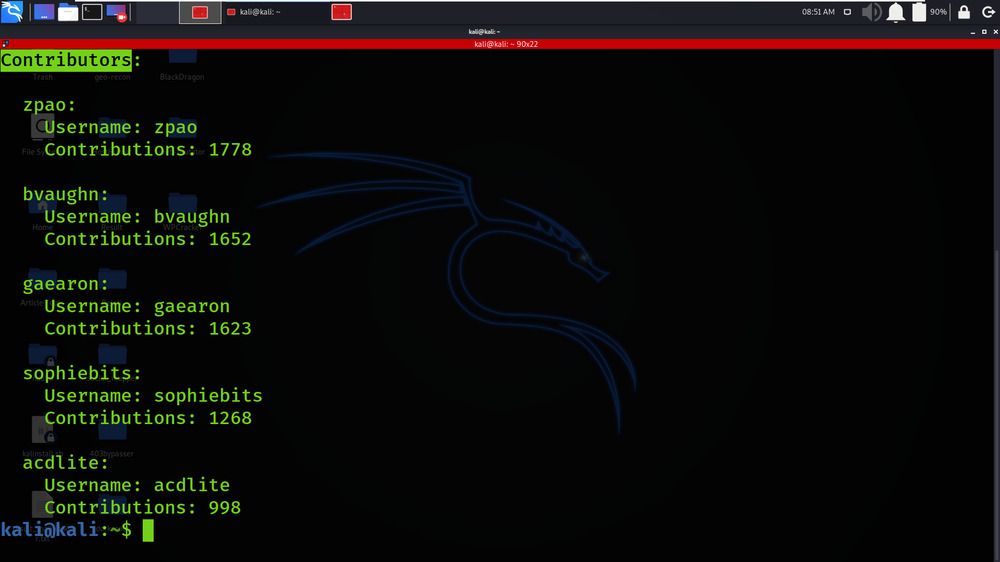
Example 1: Grab some information about Google (organization)
gitem organization google
In this example, information about google organizations is being searched on the GitHub platform.
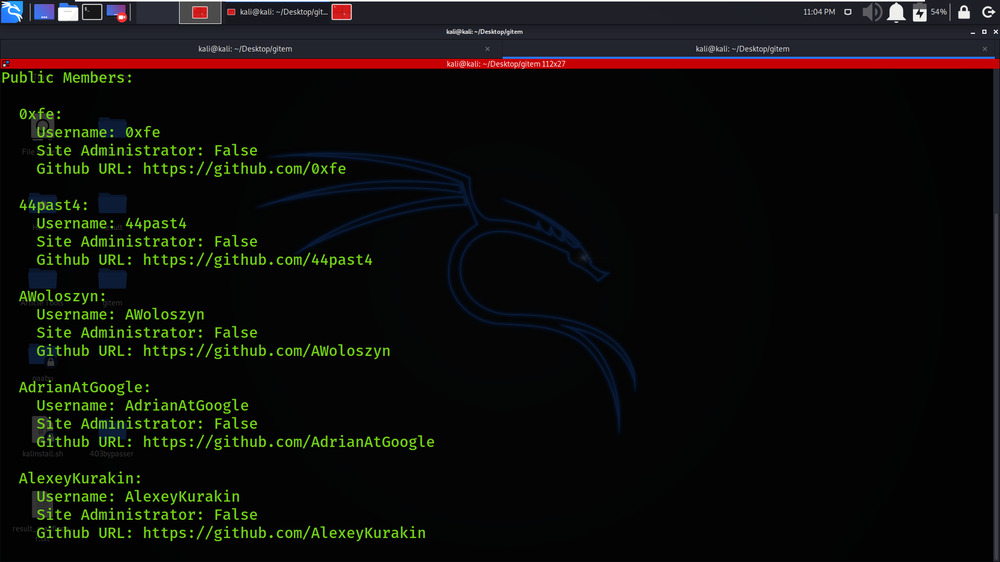
The public Member’s list is shown in the below screenshot.
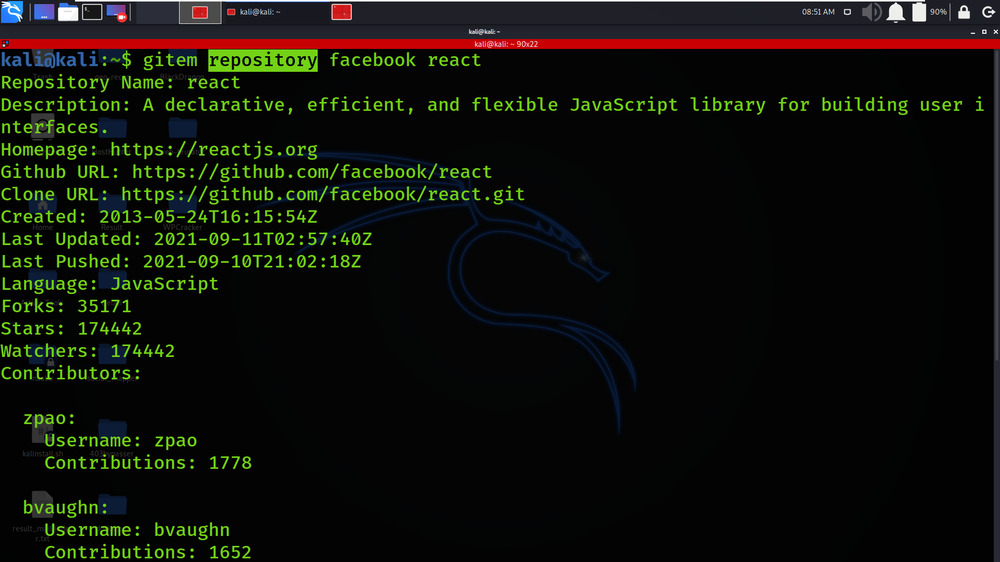
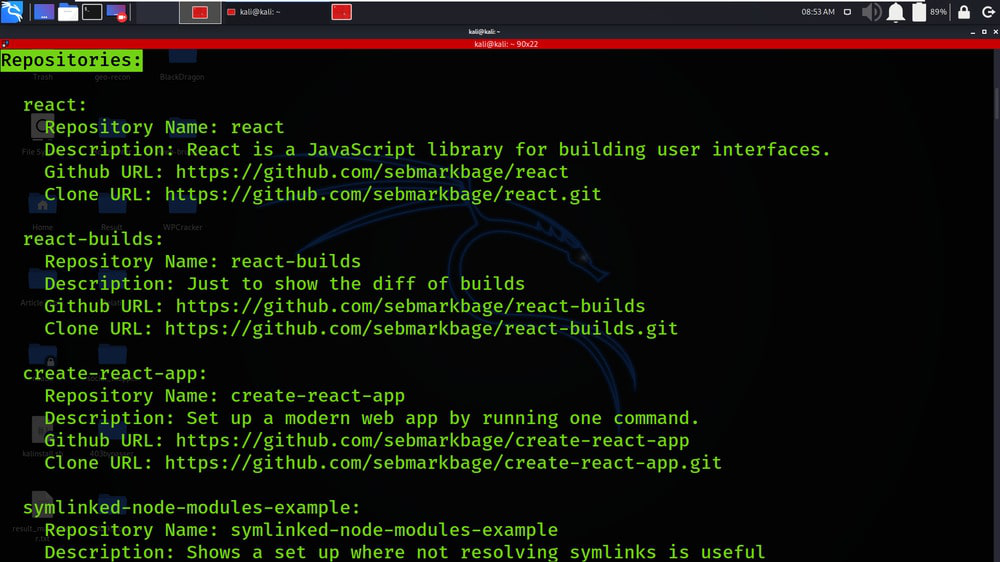
Example 2: Drill down into a certain repository (repository)
gitem repository facebook react
In this example, we will get the specific repository details that contain the react reference.
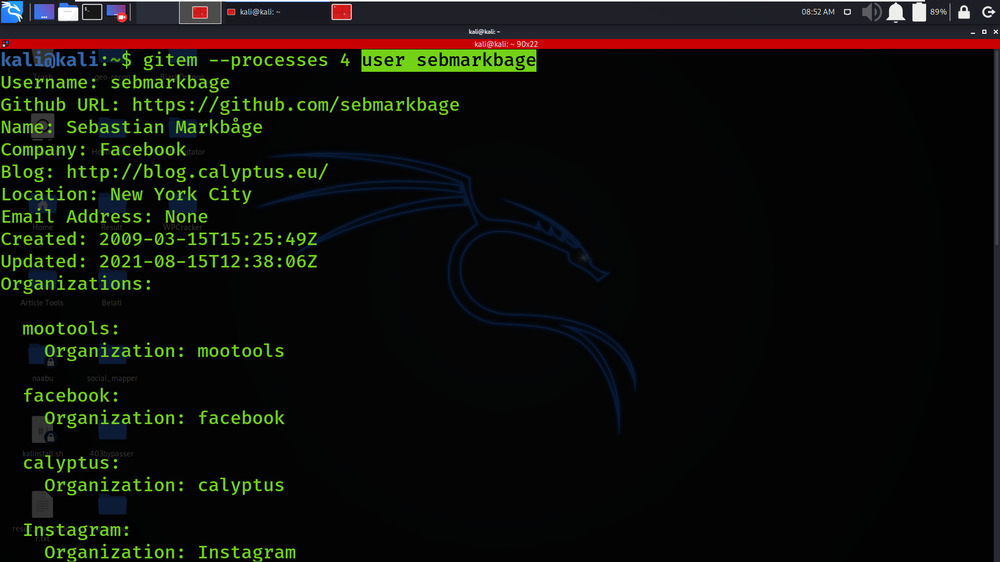
Example 3: We can analyze specific users (user)
gitem --processes 4 user sebmarkbage
In this example, we are searching for information about the specific users on GitHub, we have got the organizations list in which the user is related and also we have got the Repositories for which the user is a contributor.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...