Diversity and its Types
Last Updated :
01 Mar, 2024
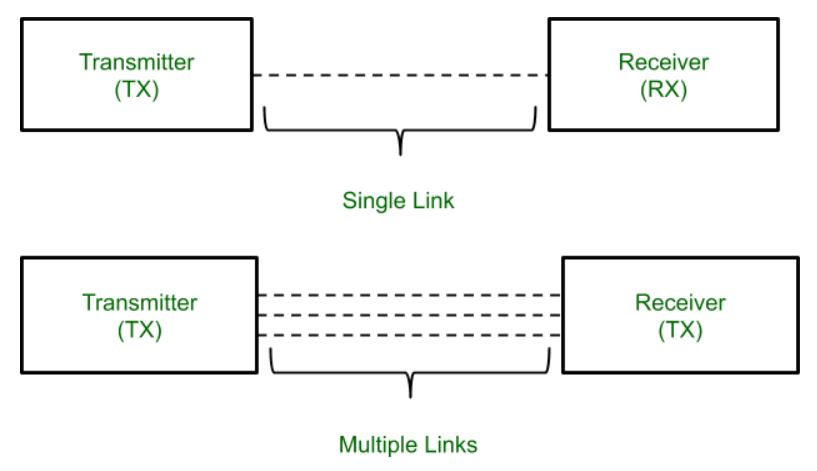
Superposition of multiple signals at the receiver causes random amplitude variation which is known as Fading. A mechanism that is used to decrease the effect of fading is called Diversity. It is used to compensate for fading channel impairments. In Diversity mechanism, multiple copies of the same data are transmitted to the receiver through multiple paths or channels and the decision is made by the receiver without knowing the transmitter.
Types of Diversity
1. Space Diversity: Replica of same signal is transmitted through different antenna. Space should be between adjacent antenna so that channel gain will be independent of signal path. Space diversity may give a path that avoid shadowing and also decrease the large scale fading. Space diversity offer different path without an increase in transmitter power or bandwidth.
Space Diversity Reception Methods
- Selection diversity : The highest instantaneous SNR(Signal-Noise Ratio) branch is connected to the demodulator. Antenna signal themselves could be sampled and the best one sent to a single demodulation.
- Feedback diversity : N-signals are scanned on the receiver side until one is found to be above a predetermined threshold. Signal is received until it falls below threshold scanning process is again initiated.
- Maximal Ratio Combining Technique: Signal from all of the N-branches are weighted according to the SNR’s and then summed. Signal must be co-phased. Output SNR = Sum of the individual SNR’s.
- Equal gain combining technique: Branch weight are all set to unity. Signal from each antenna is co-phased. Make use of energy in all branches. Performance is marginally inferior to MRC and superior to selection diversity.
2. Time Diversity: Time diversity is obtained by re-transmitting the same signal at separate interval of time. The re-transmission interval should be less than the coherence time. Time Diversity also does not require any increase in the transmission power.
Time Diversity can be realized in different ways:
• Repetition coding
• Automatic Repeat Request
• Combination of interleaving and coding
3. Frequency Diversity: Frequency diversity is obtained by transmitting the same information on more than one carrier frequency or transmitting the same signal over different carrier frequency. In Frequency Diversity only one antenna is needed. It requires large bandwidth and more number of receivers hence high cost.
4. Polarization Diversity: Polarization Diversity require two transmitter and two receiving antennas with different polarization. The transmission wave with two different polarization constitute two different paths. This provide only two different diversity branches. Polarization Diversity uses half power by dividing the power between two different polarized antennas.
5. Angular Diversity: It is also known as pattern diversity. This diversity allows the identical antennas to be located at same location but with a different pattern. These two co-located antennas with different patterns will provide a diverse path for multipath signal. It enhances the decorrelation of signal at closely spaced antennas.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...