Difference between Tor and VPN
Last Updated :
30 Sep, 2022
Tor and VPN are used to protect privacy when you are connected to the world through online. TOR and VPN contain their own specific features both of them come with some advantages and disadvantages. Choosing between them is depends on your task, in this article we will discuss the differences between them and highlight the advantages and disadvantages of both with the proper description.
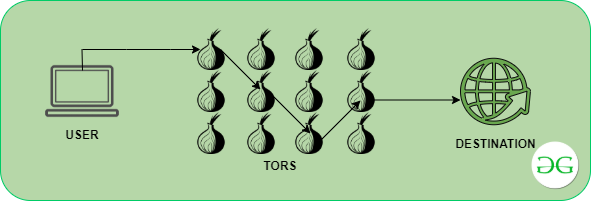
Tor: It allows users to protect their privacy and security while using the internet. It provides anonymity to its users. By using Tor no server can know your identity and what you do on the internet. It has multiple layers of encryption. It passes information between randomly selected nodes. While every node knows about where the signal begins and where it’s going, it can’t picture the entire path. Means each node only have two address source and destination. It is an onion routing.
- Working Concept: Tor takes a shot at the idea of ‘onion directing’ strategy in which the client information is first scrambled and afterward moved through various transfers present in the Tor network, subsequently making multi-layered encryption, in this manner guarding the identity of the client. One encryption layer is decoded at each progressive Tor relay, and the rest of the information is sent to any irregular relay until it arrives at its destination server. For the destination server, the last Tor node relay i.e. exit relay shows up as the starting point of the information like the below diagram.
- Advantage:
- The Tor is Complete anonymity.
- Tor protects you from hackers by hiding your ip they can not trace you.
- It is very difficult to shut down publicly sponsored thats why the network is distributed.
- Tor has a privacy-conscious search engine.
- Disadvantage:
- Some firewalls block requests sent via Tor.
- It is very slow compare to any VPN because it uses so many layers to protect your privacy.
- Tor has low device compatibility.
- Data isn’t encrypted. Data is conveyed anonymously, but the browser software contains vulnerabilities, particularly when seeing HTTP sites rather than encrypted HTTPS ones.
VPN: VPN stands for Virtual Private Network. It creates a secure and encrypted connection over a less secure network. When a user connects to a VPN, all his/her data and traffic get routed through that network. By connecting to a VPN, the IP address also gets changed with the server’s address. Its servers are located in multiple countries around the world.
- Working Concept: A VPN works by directing the user’s device’s internet connection through a picked VPN’s private server as opposed to ISP so when the user’s information is transmitted to the web. It originates from the VPN instead of user’s PC. The VPN goes about as a go-between of sorts as user interfaces with the web, in this manner concealing the user’s IP address and securing the identity. A VPN makes a private tunnel from PC to the web and hides essential information through encryption.

- Advantage:
- Compatible with most devices.
- Completely anonymous.
- Provides top-of-the-line encryption protocols.
- Helps to bypass Geo-Blocks.
- Prevents Bandwidth Throttling.
- Bypass Firewalls.
- Disadvantage:
- VPN has Weak encryption.
- VPN is not completely free you have to pay to use.
- Software failures problem.
- Using wrong VPN can put privacy in danger.
- VPN connection breaks some times.
- In VPN it is difficult to check the quality of encryption.