Difference between Steganography and Cryptography
Last Updated :
11 Apr, 2024
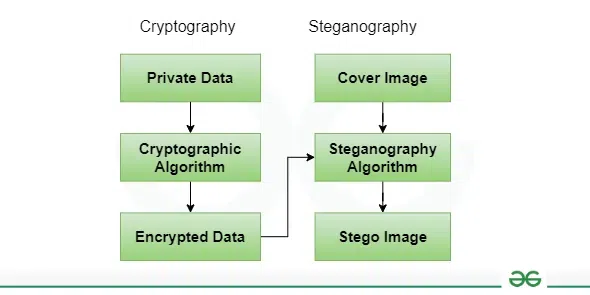
Steganography and cryptography are critical components of network security. Network security has emerged as an essential part of today’s communication infrastructure. There was an urgent need for network security to protect confidentiality and data integrity. It protects the user against unauthorized access. Steganography hides communication traces, while cryptography uses encryption to make the message unreadable.
Cryptography vs Steganography
What is Steganography?
Steganography is a method in which a secret message is hidden in a cover media. Steganography means covered writing. Steganography is the idea of preventing secret information by creating suspicion. Steganography is less popular than Cryptography. In steganography, the structure of data is not usually altered. The forms of steganography are:
- Text
- Audio
- Video
- Images
- Network or Protocol
What is Cryptography?
Cryptography means secret writing. In cryptography, the sender does not send a message directly to the receiver, before sending information to the receiver information or plain text is converted into cipher text by using some encryption algorithm then sent to the receiver and the receiver decrypts the cipher text into plain text to read the original information. It is of two types:
Difference between Steganography and Cryptography
| Basis |
Steganography |
Cryptography |
| Definition |
Steganography means covered writing. |
Cryptography means secret writing. |
| popularity |
Steganography is less popular than Cryptography. |
While cryptography is more popular than Steganography. |
| Attack Name |
The attack’s name in Steganography is Steganalysis. |
In cryptography, the Attack’s name is Cryptanalysis. |
| Data Alteration |
In steganography, the structure of data is not usually altered. |
While in cryptography, the structure of data is altered. |
| Security Principles |
Steganography supports Confidentiality and Authentication security principles. |
Cryptography supports Confidentiality and Authentication security principles as well as Data integrity and Non-repudiation. |
| Visibility |
In steganography, the fact that a secret communication is taking place is hidden. |
While in cryptography only a secret message is hidden. |
| Mathematical Involvement |
In steganography, not many mathematical transformations are involved. |
Cryptography involves the use of number theory, mathematics, etc. to modify data |
| Information Handling |
In Steganography the information is hidden. |
In cryptography, the information is transformed. |
| Information Visibility |
The hidden information is not visible. |
Transformed information is visible. |
| Security Services |
Steganography Provides Confidentiality only. |
Cryptography Provides Confidentiality, Integrity, Non-repudiation. |
| Algorithms |
Steganography doesn’t have specific algorithms. |
Cryptography has Various recognized and approved algorithms. |
| Goal |
The goal of steganography is to make the information invisible to anyone who doesn’t know where to look or what to look for |
The main goal of cryptography is to keep the contents of the message secret from unauthorized access. |
Frequently Asked Questions on Steganography and Cryptography – FAQs
Which method is commonly accomplished using steganography?
Image steganography.
What are some challenges in cryptography?
Challenges include protecting cryptographic algorithms from attacks, securely handling cryptographic keys, and combining security with usability and performance.
What is the major weakness of steganography?
Steganography systems’ limited capacity makes it difficult to transmit private data over the internet.
What are the main goals of cryptography?
- Confidentiality
- Integrity
- Authentication
- Non-Repudiation
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...