Difference between Information Security and Network Security
Last Updated :
22 Feb, 2023
Introduction :
Information Security refers to the measures taken to protect and secure information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction. This includes protecting data and information in physical, technical and administrative ways to ensure its confidentiality, integrity and availability. Information security is important in protecting against cyber attacks, theft of sensitive information, and ensuring privacy.
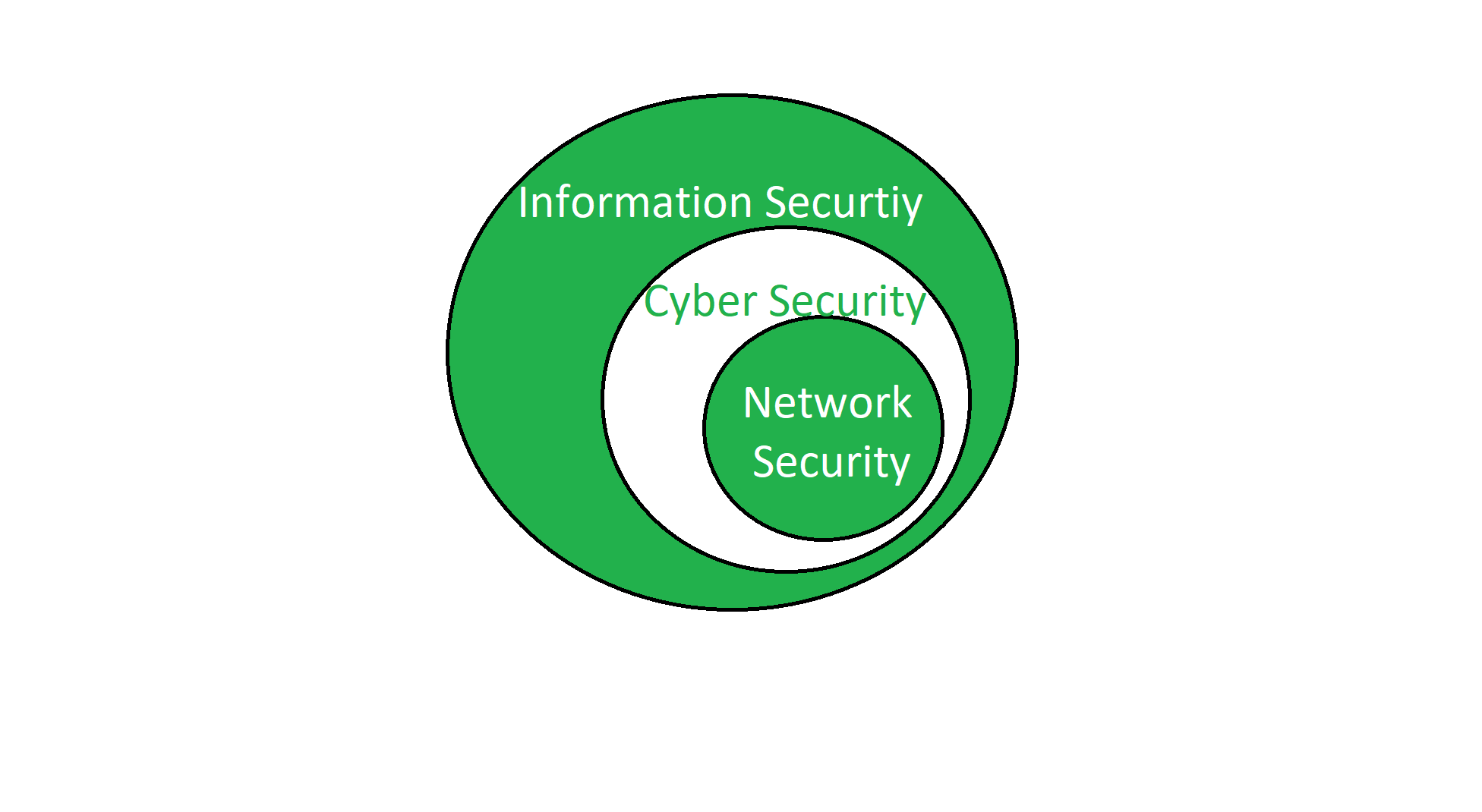
Information Security is the measures taken to protect the information from unauthorized access and use. It provides confidentiality, integrity, and availability. It is the superset that contains cyber security and network security. It is necessary for any organization or firm that works on a large scale.
Examples and inclusion of Information Security are as follows:
- Procedural Controls
- Access Controls
- Technical Controls
- Compliance Controls
Network Security is a subfield of information security that focuses on the protection of networks, including both hardware and software components, from unauthorized access, misuse, and damage. Network security aims to protect the confidentiality, integrity and availability of data transmitted over a network. Common network security measures include firewalls, intrusion detection and prevention systems, encryption, and secure protocols such as VPN and HTTPS. Network security is essential for protecting sensitive information transmitted over the internet, as well as for maintaining the integrity and availability of networked systems and devices.
Network Security is the measures taken by any enterprise or organization to secure its computer network and data using both hardware and software systems. This aims at securing the confidentiality and accessibility of the data and network. Every company or organization that handles a large amount of data, has a degree of solutions against many cyber threats.
Examples and inclusion of Network Security are as follows:
- Firewall
- Network Segmentation
- Remote Access VPN
- Email Security
- Intrusion Prevention Systems (IPS)
- Sandboxing
- Hyperscale Network Security.
- Data Loss Prevention (DLP)
Difference between Information Security and Network Security:
| Parameters |
Information Security |
Network Security |
| Definition |
Information Security refers to the protection of information and information systems from unauthorized access, use, disclosure, disruption, modification, or destruction |
Network Security focuses on the protection of data transmitted over networks from unauthorized access and malicious attacks. |
| Scope |
Information Security has a broader scope, as it covers the protection of all types of information, regardless of the means of transmission. |
Network Security is limited to the protection of data transmitted over networks. |
| Focus |
Information Security focuses on protecting the confidentiality, integrity and availability of information and information systems |
Network Security focuses specifically on the confidentiality and integrity of data transmitted over a network. |
| Threats |
Information Security is concerned with protecting against data breaches, theft of sensitive information, and unauthorized access to information systems |
Network Security is focused on threats such as malware, hacking, and denial-of-service attacks that target networked systems. |
| Solutions |
Information Security relies on a variety of solutions, including access controls, encryption, secure backups, and disaster recovery plans. |
Network Security relies on specific technologies such as firewalls, intrusion detection and prevention systems, and encryption protocols to secure data transmitted over networks. |
| Data |
It protects information from unauthorized users, access, and data modification. |
It protects the data flowing over the network. |
| Part of |
It is a superset of cyber security and network security. |
It is a subset of cyber security. |
| Protection |
Information security is for information irrespective of the realm. |
It protects anything in the network realm. |
| Attack |
It deals with the protection of data from any form of threat. |
It deals with the protection from DOS attacks. |
| Scope |
It strikes against unauthorized access, disclosure modification, and disruption. |
Network Security strikes against trojans. |
| Usage |
It provides confidentiality, integrity, and availability. |
It provides security over the network only. |
| Ensures |
Information security ensures to the protection of transit and stationary data. |
Network security ensures to protect the transit data only. |
| Deals with |
It deals with information assets and integrity, confidentiality, and availability. |
It secures the data traveling across the network by terminals. |
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...