Difference between Encryption and Cryptography
Last Updated :
05 Jan, 2024
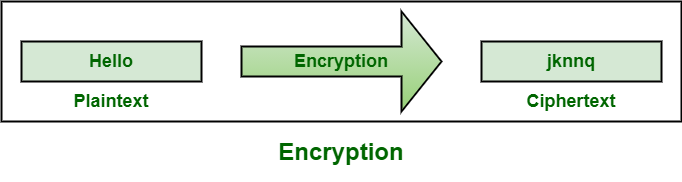
1. Encryption :
Encryption, as name suggests, is generally a technique that is used to conceal message using algorithms. It is fundamental application of cryptography that encodes a message with an algorithm. It generally helps to protect private information, sensitive data, and enhance security of communication among client apps and servers. It is considered one of most effective and popular data security techniques.
Example :
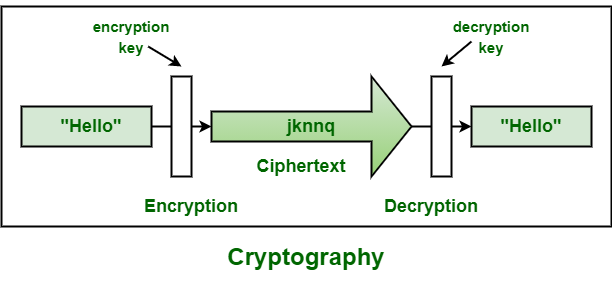
2. Cryptography :
Cryptography, as name suggests, is generally study of methods like encryption. Its main objective is to provide methods simply to secure and protect information and communications using encryption and related techniques. It simply allows one to store sensitive information or transmit it across insecure networks so that it cannot be read or accessed by anyone except intended recipient. Its functions include authentication, nonrepudiation, confidentiality and integrity.
Example :
Difference between Encryption and Cryptography :
| It is a process of encoding message or information so that only authorized parties can have access to it. |
It is study of techniques such as encryption for secure communication in presence of third parties. |
| It is considered as principal application of cryptography. |
It is considered as art of creating codes using techniques of encryption and decryption. |
| It simply uses algorithm to encrypt data and secret key to decrypt it. |
It simply provides methods of protecting data through encryption and its related processes. |
| It is all about mathematical and algorithmic in nature. |
It is all about techniques and technologies in nature. |
| Its main purpose is confidentiality that means concealing content of message by translating it into code. |
Its main purpose is to apply complex mathematics and logic to design strong encryption methods. |
| Types of encryption includes symmetric and asymmetric encryption. |
Types of cryptography includes symmetric key cryptography and asymmetric key cryptography. |
| It provides security to data all times, maintains integrity, protects privacy, protects data across devices, etc. |
In provides techniques like encryption techniques that can guard information and communication, cryptographic technique like MAC and digital signatures to protect information against spoofing and forgeries. |
| It follows same approach with some terms like ciphertext, plaintext, and cipher. |
It has symmetric and asymmetric version with concept of shared and non-shared key. |
| It is useful to modern data security such as digital signatures and protect sensitive electronic data such as emails and passwords. |
It is useful in electronic commerce, military communications, chip-based card payments, digital currencies, time stamping, etc. |
Share your thoughts in the comments
Please Login to comment...