Thomas Write Rule in DBMS
Last Updated :
22 May, 2023
The “write rule” in database management systems (DBMS) refers to a principle that governs how changes to the database are handled. Specifically, the write rule states that any modification to a database must be written to disk before control is returned to the user.
In other words, when a user executes a command that modifies the database (such as an update or delete statement), the DBMS must ensure that the change is permanently saved to disk before the user is allowed to continue with other actions. This ensures that the database remains consistent and durable, even in the event of system failures or crashes.
The Write Rule is one of the fundamental principles of database management and is an important part of ensuring data integrity and reliability
Timestamp Ordering Protocol states that if Ri(X) and Wj(X) are conflicting operations then Ri (X) is processed before Wj(X) if and only if TS(Ti) < TS(Tj). Whenever a schedule does not follow a serializability order according to the Timestamp, a user generally rejects it and rollback the Transaction. Some operations on the other hand are harmless and can be allowed.
Thomas Write Rule allows such operations and is a modification of the Basic Timestamp Ordering protocol. In Thomas Write Rule users ignore outdated writes. Moreover, of all the Concurrency Protocols that have been discussed, Concurrency is imposed on Schedules that are Conflict Serializable, in Thomas Write Rule, the most important improvement is a user can achieve Concurrency with View Serializable schedules.
First, let’s state what is Thomas Write Rule and then what are modifications and improvements it succeeds over the Basic TO protocol.
Thomas Write Rule
Thomas Write Rule does not enforce Conflict Serializability but rejects fewer Write Operations by modifying the check Operations for W_item(X)
- If R_TS(X) > TS(T), then abort and roll back T and reject the operation.
- If W_TS(X) > TS(T), then don’t execute the Write Operation and continue processing. This is a case of Outdated or Obsolete Writes. Remember, outdated writes are ignored in Thomas Write Rule but a Transaction following the Basic TO protocol will abort such a Transaction.
- If neither the condition in 1 or 2 occurs, then and only then execute the W_item(X) operation of T and set W_TS(X) to TS(T).
Outdated Write Example
The main update in Thomas Write Rule is ignoring the Obsolete Write Operations. This is done because some transaction with a timestamp (TS) greater than TS(T) (i.e., a transaction after T in TS ordering) has already written the value of X. Hence, logically user can ignore the Write(X) operation of T which becomes obsolete. Let us see this through an example:
Suppose a user has a schedule in which two transactions T1 and T2. Now, TS(T2) < TS(T1). This means T1 arrived after T2 and hence has a larger TS value than T2. This implies that the serializability of the schedule allowed is T2 –> T1. Consider the partial schedule given below:
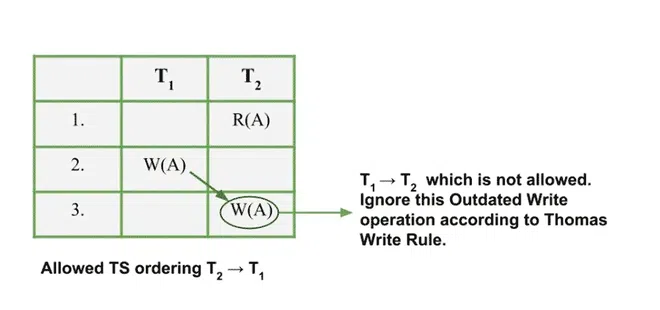
Example of Outdated Write
Obsolete Writes are hence ignored in this rule which is in accordance with the 2nd protocol. It seems to be more logical as users skip an unnecessary procedure of restarting the entire transaction. This protocol is just a modification to the Basic TO protocol.
| T1 |
T2 |
| R(A) |
|
| |
W(A) |
| |
Commit |
| W(A) |
|
| Commit |
|
The above table is showing a Serializable Schedule that is not a Conflict Serializable.
| T1 |
T2 |
| R(A) |
Commit |
| W(A) |
|
| Commit |
|
The above table is showing a Conflict Serializable Schedule.
Difference Between Basic TO Protocol and Thomas Write Rule
Suppose a user has a schedule in which two transactions T1 and T2. Now, TS(T2) < TS(T1). This implies that the serializability of the schedule allowed is T2 –> T1. Consider the two protocols, and let us see what types of Operations will be allowed and not allowed under them. Ri(A) implies Read and Wi(A) implies Write operation. Now, let us look at the types of partial schedules allowed in both Basic TO and Thomas Write Rule, you’ll understand the difference in operations of both protocols. User distinguish in operations Allowed and Not Allowed in both of the Protocols.
| Basic TO Protocol |
Thomas Write Rule |
- Not Allowed
- R1(X) W2(X)
- W1(X) R2(X)
- W1(X) W2(X)
- Allowed
- All operations where T2 occurs before T1.
- R1(X) R2(X)
|
- Not Allowed
- Allowed
- All operations where T2 occurs before T1.
- Outdated Writes: W1(X) W2(X)
- R1(X) R2(X)
|
Thus, from the above list, this modification is used in Thomas Write Rule in comparison to the Basic TO protocol.
Features of Thomas Write Rule
The Thomas Write Rule, also known as the Write-Ahead Logging (WAL) protocol, has several key features that make it an important principle of database management systems:
- Durability: The Thomas Write Rule ensures that any modifications to the database are permanently saved to disk before the transaction is considered complete. This means that even in the event of a system failure or crash, the database can be recovered to a consistent state.
- Atomicity: The Thomas Write Rule is part of a larger principle of atomicity, which states that a transaction must either be complete in its entirety or be completely rolled back in the event of an error. By ensuring that modifications to the database are written to disk before a transaction is considered complete, the Thomas Write Rule helps to enforce atomicity.
- Concurrent Access: The Thomas Write Rule allows multiple users to access the database concurrently, while still ensuring that the database remains consistent and durable. This is accomplished through a variety of mechanisms, such as locking and transaction isolation levels.
- Performance: While the Thomas Write Rule does require that changes be written to disk before control is returned to the user, modern database systems are able to optimize the process to minimize the impact on performance. For example, many systems use a technique called “write-ahead logging” to batch changes together and write them to disk in an efficient manner.
Conclusion
Overall, the Thomas Write Rule is an important principle of database management that helps to ensure data integrity, reliability, and performance.
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...