CT-EXPOSER – Uncover Hidden Subdomains and Reveal Internal Server Information
Last Updated :
28 Jul, 2021
Certificate Transparency(CT) is an open framework used to monitor SSL(Secure Sockets Layer) Certificates. Domain owners may discover it beneficial to watch certificate supplying for their domain and learn mississued certificates. The Certificate Transparency(CT) framework means the domain owner can discover mississued certificates quickly and effectively compared to the old method where criminal certificates could be left in the wild wreak destruction for weeks or even months before they are detected.
What Is a Certificate Trust Log?
Each Certificate Transparency has a log or record, collecting all publicly trusted digital certificates. These certificates consist of vital information like the subject, information about the certificate issuer, and public key. These logs or records keep this information stored in a Cryptographically format, the most secure way. These certificates have only permission to append or add the new description rather than modifying or deleting the log is not allowed. As said, Cryptographically secured” are those records that help to append the certificates in cryptographic aspect like Merkle hash tree, only allowing for systematic and secure verification.
What is CT-Exposer Tool?
CT-exposer tool is a python language-based tool used to find hidden and subdomains of any target domain. CT-exposer is the best tool used in the phase of Information Gathering. The primary purpose could be anything to use this tool. It can return you some vital information about a target domain and can be used to perform attacks like subdomain takeover, open redirection, etc.

How does CT Exposer work?
CT Exposer will ask a question to Ct logs and check for DNS lookup to check the available domain in DNS. According to CT Exposer’s claim, it can detect the domain which is not obtainable on google even after Google dork/Google hacking.
Installation of CT-EXPOSER tool in Kali Linux
Make Sure You have Python Installed on your System,as this is python-based tool.
Click to Install : Python Installation Steps on Linux
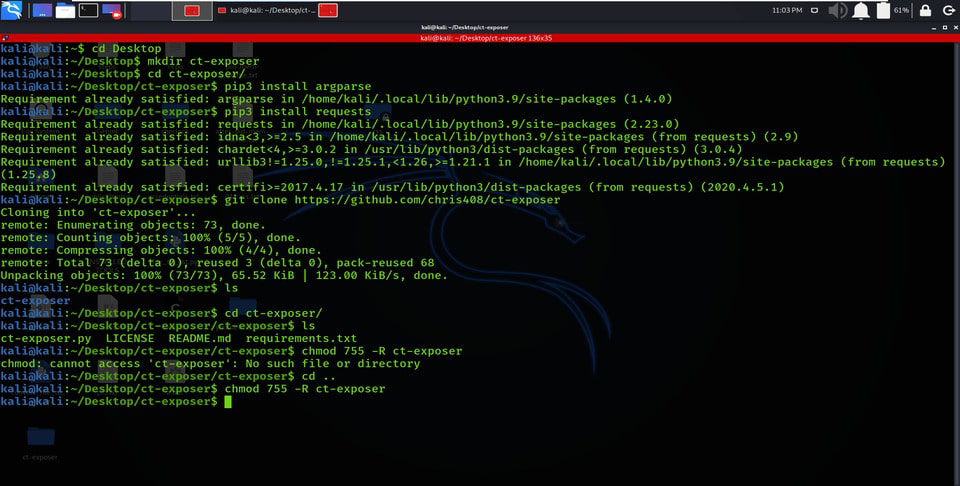
Step 1: Fire up your Kali Linux terminal and move to Desktop using the following command.
cd Desktop

Step 2: You are on Desktop, now create a new directory called ct-exposer using the following command. In this directory, we will complete the installation of the ct-exposer tool.
mkdir ct-exposer

Step 3: Now switch to ct-exposer directory using the following command.
cd ct-exposer

Step 4: You have to install the first basic requirement (argparse package) which is used by this tool. Use the below command to install.
pip3 install argparse

Step 5: You have to install the second basic requirement(requests) which is used by this tool. Use the below command to install.
pip3 install requests

Step 6: Now you have to install the tool. You have to clone the tool from Github.
git clone https://github.com/chris408/ct-exposer

Step 7: The tool has been downloaded successfully in the ct-exposer directory. Now list out the contents of the tool by using the below command.
ls

Step 8: You can observe that there is a new directory created of the ct-exposer tool that has been generated while we were installing the tool. Now move to that directory using the below command:
cd ct-exposer

Step 9: Once again to discover the contents of the tool, use the below command.
ls

Step 10: You can observe various files of the tool here. Now you have to first give permission to the tool to make it usable. To give permissions follow the below command.
chmod 755 -R ct-exposer
Step 11: Now we are done with our installation, Use the below command to view the help (gives a better understanding of tool) index of the tool.
python3 ct-exposer.py --help

Working with CT-EXPOSER Tool
Example 1: Enumerating Subdomains
The tool has been downloaded successfully using this tool you can easily check the hidden subdomains of the target domain which are not identified by Google Dorking also. Now here are some examples to use the CT-EXPOSER tool.
python3 ct-exposer.py -d geeksforgeeks.org

CT-EXPOSER has also searched subdomains that don’t have DNS records.

Visiting the doubtful subdomain on a web browser. https://udevtest.geeksforgeeks.org is the Administrative subdomain which has limited users permission to access. So being Hacker you can try to Bypass this wall and access the data without permissions

Example 2: Subdomains with DNS That Does Not Resolve
python3 ct-exposer.py -d priceline.com
1. Subdomains of priceline.com are identified.

2. There is no IP address for the selected Subdomain (it menas it is Subdomain with DNS that does not resolve

3. After visiting the subdomain there is no response from the server.

Example 3: Subdomains with DNS That Does Resolve
1. We can see that this subdomain has an IP address which means that, it is ( Subdomains with DNS That Does Resolve)

2. After visiting the Subdomain we can see the response from the server

3. One more subdomain that resolves DNS

4. After Visiting the subdomain we get a response from the server

Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...