Brutespray – Port Scanning and Automated Brute Force Tool
Last Updated :
23 Sep, 2021
Brute-Forcing is the technique of matching the credentials like Usernames, Passwords, OTPs for unauthenticated access to the target domain. The list of words are been tested against the target to get the exact credentials. All this process is done through automated tools.
Brutespray is an automated tool that is used to perform brute-forcing for every possible way like Credentials Brute-Forcing, FTP brute-forcing, etc. The Brutespray tool is developed in the Python language which comes with tags-based usage and also interactive usage. After Scanning the target from Nmap the results are to be inputted to the tool for performing brute-forcing. This tool supports GNMAP/XML output file to Brute force Nmap open port services with default credentials using Medusa or Use your dictionary to gain access.
Note: Make Sure You have Python Installed on your System, as this is a python-based tool. Click to check the Installation process: Python Installation Steps on Linux
Installation of Brutespray Tool on Kali Linux OS
Step 1: Use the following command to install the tool in your Kali Linux operating system.
git clone https://github.com/x90skysn3k/brutespray.git

Step 2: Now use the following command to move into the directory of the tool. You have to move in the directory in order to run the tool.
cd brutespray

Step 3: You are in the directory of the Brutespray. Now you have to install a dependency of the Brutespray using the following command.
sudo pip3 install -r requirements.txt

Step 4: All the dependencies have been installed in your Kali Linux operating system. Now use the following command to run the tool and check the help section.
python3 brutespray.py -h

Working with Brutespray Tool on Kali Linux OS
Example 1: Using Custom Wordlists
python3 brutespray.py –file results.gnmap -U user.txt -P pass.txt –threads 5 –hosts 5
In this example, we are using the custom word-lists to perform Brute-Forcing on the target domain.



Example 2: Brute-Forcing Specific Services
python3 brutespray.py –file results.gnmap –service ftp,ssh,telnet –threads 5 –hosts 5
In this example, we are only going to perform brute-forcing on ftp,ssh and telnet service.


Example 3: Specific Credentials/ Brute-Forcing Username and Password
python3 brutespray.py –file results.gnmap -u admin -p password –threads 5 –hosts 5
In this example, we will be brute-forcing with single or specified credentials.


Example 4: Continue After Success
python3 brutespray.py –file results.gnmap –threads 5 –hosts 5 -c
In this example, we will be continuing over brute-forcing attack after success also.


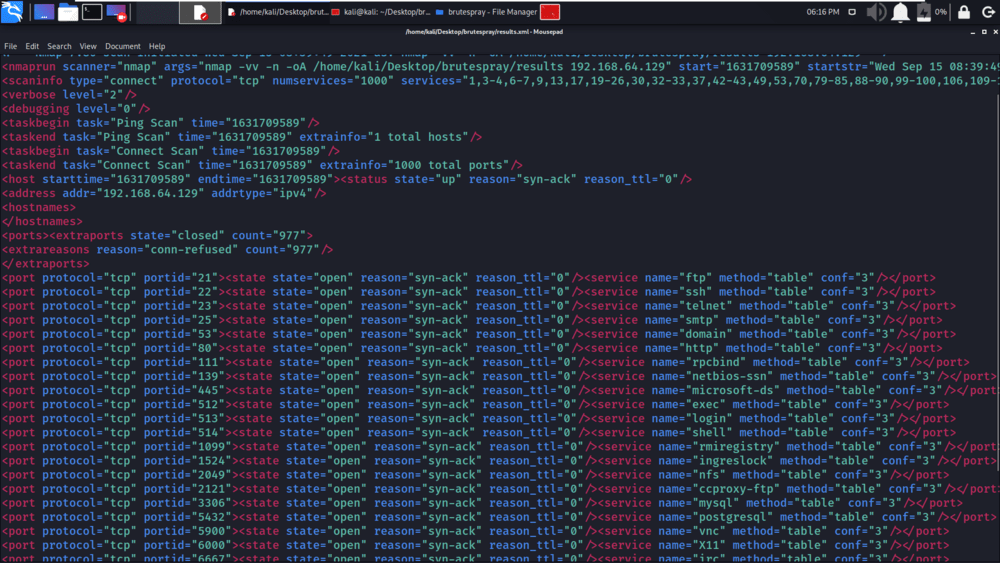
Example 5: Use Nmap XML Output
python3 brutespray.py --file results.xml --threads 5 --hosts 5
In this example, we will be using the XML file for scanning and brute-forcing.


Example 6: Brutespray Interactive Mode
python3 brutespray.py --file results.xml -i
In this example, we will be using the interactive mode of the tool Brutespray.



Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...