Bit Stuffing in Computer Network
Last Updated :
03 Nov, 2022
The data link layer is responsible for something called Framing, which is the division of stream of bits from network layer into manageable units (called frames). Frames could be of fixed size or variable size. In variable-size framing, we need a way to define the end of the frame and the beginning of the next frame.
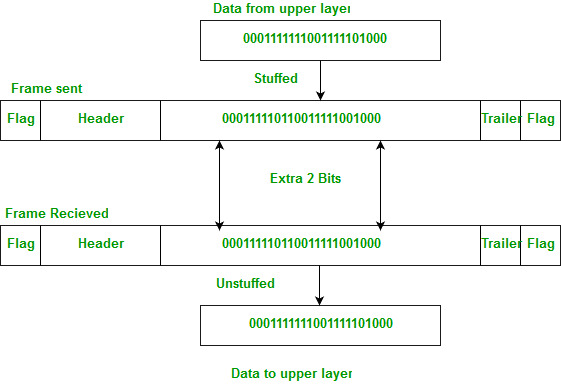
Bit stuffing is the insertion of non information bits into data. Note that stuffed bits should not be confused with overhead bits.
Overhead bits are non-data bits that are necessary for transmission (usually as part of headers, checksums etc.).
Applications of Bit Stuffing –
- synchronize several channels before multiplexing
- rate-match two single channels to each other
- run length limited coding
Run length limited coding – To limit the number of consecutive bits of the same value(i.e., binary value) in the data to be transmitted. A bit of the opposite value is inserted after the maximum allowed number of consecutive bits.
Bit stuffing technique does not ensure that the sent data is intact at the receiver side (i.e., not corrupted by transmission errors). It is merely a way to ensure that the transmission starts and ends at the correct places.
Disadvantages of Bit Stuffing:
- The code rate is unpredictable; it depends on the data being transmitted.
- The stuffed bits do not contain any information.
Example of bit stuffing –
Bit sequence: 110101111101011111101011111110 (without bit stuffing)
Bit sequence: 110101111100101111101010111110110 (with bit stuffing)
After 5 consecutive 1-bits, a 0-bit is stuffed. Stuffed bits are marked bold.
Refer for difference between Byte stuffing and Bit stuffing
Like Article
Suggest improvement
Share your thoughts in the comments
Please Login to comment...